Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Ransomware attack vectors: what your organisation needs to look out for
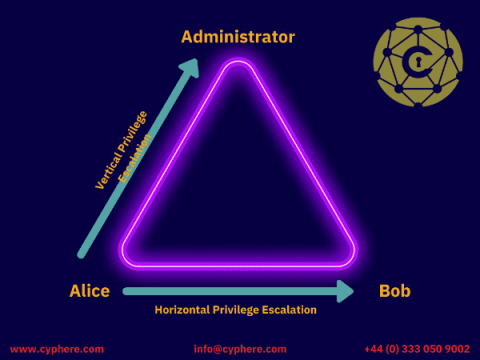
Privilege Escalation Attacks: Types, Examples and Defence
When a system is breached, compromised or exploited, the attackers never stop after getting the initial access because it doesn’t give them privileged access. And the same thing goes in an offensive security assessment, i.e. infrastructure penetration testing or a red team assessment.
API attack types and mitigations
Stop, look, listen; lock, stock, and barrel; "Friends, Romans, Countrymen..." The 3 Little Pigs; Art has 3 primary colors; photography has the rule of thirds; the bands Rush and The Police; the movie The 3 Amigos. On and on it goes - "Omne trium perfectum" – “Everything that comes in threes is perfect.” While this article doesn’t provide perfection, we’ll focus on the top three API vulnerabilities (according to OWASP).
Single Author Uploaded 168 Packages to npm as Part of a Massive Dependency Confusion Attack
Mend Supply Chain Defender reported and blocked dozens of packages from the same author. These packages targeted developers of many companies and frameworks like slack, Cloudflare, Datadog, Metamask, react, Shopify, OpenSea, Angular and more. A dependency confusion attack takes advantage of a software developer’s tendency to pull malicious code from public repositories rather than internal ones.
What is a Distributed Denial-of-Service (DDoS) attack?
If you don’t work in IT or security, there’s no need to fret about every detail of every online danger. Nevertheless, it’s worth having awareness of the strategies and techniques that criminals are using to achieve their goals online.
Enriched attack surface view, DNS filtering, and more
Taking action on your attack surface requires a complete overview of what is exposed. This includes details such as open – and previously open! – ports, DNS records, and when the asset was last seen. These details help security teams respond more effectively to issues as they occur in production. It’s now possible for Surface Monitoring customers to drill down into an asset with the new Details page, which you can access by selecting an asset from the Attack Surface view.
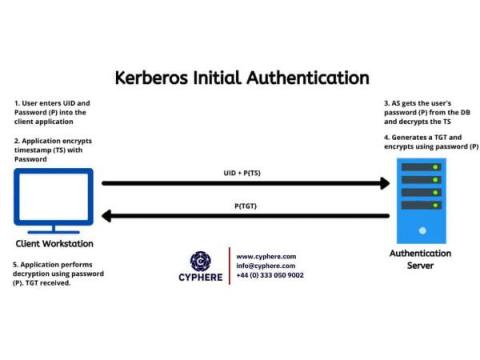
Kerberos Authentication: Basics to Kerberos attacks
Developed by MIT, Kerberos Authentication Protocol is the default authentication service for Microsoft Active Directory. It is named after the three-headed dog (Cerberus) found in Greek mythology, because the security protocol involves three major steps in the entire authentication process. Although Kerberos is a technology used by Microsoft Windows, by default, its implementations in other operating systems, such as Linux, FreeBSD and macOS, are also present.
Conti ransomware incapacitates Costa Rica's government: The FBI, CISA, the NSA, and Secret Service recommend mitigation strategies
Weeks after President Rodrigo Chaves Robles became Costa Rica’s 49th president, he had to tackle the country’s largest cyberattack ever. Costa Rica declared a state of emergency following a series of detrimental ransomware attacks carried out by the Conti ransomware gang.