Performance improvements, snappier ports, and spring cleaning
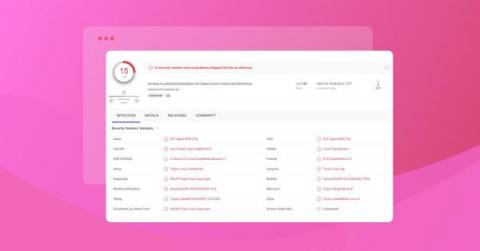
The vulnerabilities page allows you to see all findings across your attack surface. This includes simple filters that let you specify what you want to focus on, including the level of severity, which domains you want to look at, and whether it was found in the past week or the past month.