Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Revisiting 5 Concerning Cyber Trends And Statistics Over The Past Year
Managing Your Assets with Tripwire Enterprise
Asset management is a tricky subject. In many cases, organizations have no idea about how many assets they have, let alone where they are all located. Fortunately, there are tools that can assist with reaching your asset management goals. While Tripwire Enterprise (TE) is great for detecting unauthorized changes on your system and also for ensuring your systems are hardened (as well as stay hardened), you must first get a handle on managing the assets that you’re monitoring.
How Calico Cloud's runtime defense mitigates Kubernetes MITM vulnerability CVE-2020-8554
Since the release of CVE-2020-8554 on GitHub this past December, the vulnerability has received widespread attention from industry media and the cloud security community. This man-in-the-middle (MITM) vulnerability affects Kubernetes pods and underlying hosts, and all Kubernetes versions—including future releases—are vulnerable. Despite this, there is currently no patch for the issue.
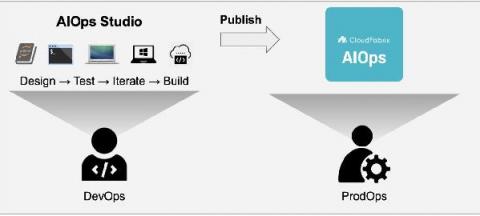
Taming the Data Problem and Accelerating AIOps implementations with Robotic Data Automation (RDA)
How to Avoid Phishing Scams
Countless phishing attempts are made every day, and with Covid-19 causing many organisations to move to remote working, phishing attacks have massively increased over the last year. In fact, last year’s Phishing and Fraud Report found that phishing incidents rose 220% during the height of the global pandemic compared to the yearly average.
Leveraging Employee Monitoring Software to Achieve Regulatory Compliance
As digital security and data privacy become increasingly caustic issues, regulatory compliance is exceedingly challenging. Not only are various regions implementing unique standards, but industries, municipalities, and platforms are issuing new guidelines as well. While CTOs have many solutions for ensuring system compliance, the human element remains more difficult to oversee, mandate, and manage.
What's the Most Powerful Tool in Your Security Arsenal?
Trying to work out the best security tool is a little like trying to choose a golf club three shots ahead – you don’t know what will help you get to the green until you’re in the rough. Traditionally, when people think about security tools, firewalls, IAM and permissions, encryption, and certificates come to mind. These tools all have one thing in common – they’re static.
Threat Hunting with Threat Intelligence
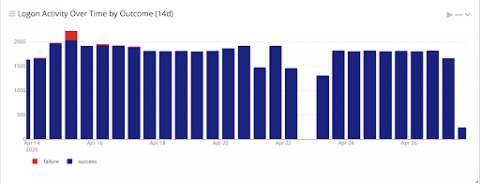
With more people working from home, the threat landscape continues to change. Things change daily, and cybersecurity staff needs to change with them to protect information. Threat hunting techniques for an evolving landscape need to tie risk together with log data. Within your environment, there are a few things that you can do to prepare for effective threat hunting. Although none of these is a silver bullet, they can get you better prepared to investigate an alert.
5 ways to prevent code injection in JavaScript and Node.js
Writing secure code in a way that prevents code injection might seem like an ordinary task, but there are many pitfalls along the way. For example, the fact that you (a developer) follow best security practices doesn’t mean that others are doing the same. You’re likely using open source packages in your application. How do you know if those were developed securely? What if insecure code like eval() exists there? Let’s dive into it.
Learn About CloudCasa - Kubernetes and Cloud Database Protection as a Service
CloudCasa™, a simple, scalable, cloud-native data protection service that supports all leading Kubernetes distributions and managed services, is now generally available through the SUSE Rancher™ Apps & Marketplace. With increasing adoption of cloud database services, CloudCasa adds cloud database support starting with Amazon RDS to its Kubernetes data protection service – addressing both Kubernetes and RDS support in a single data protection service.