Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
OWASP Top 10: Cross-Site Scripting (XSS) Security Vulnerability Practical Overview
Cross-site scripting (XSS) is #7 in the current OWASP Top Ten Most Critical Web Application Security Risks – and the second most prevalent web application vulnerability. It is thought to exist in two-thirds of all applications.
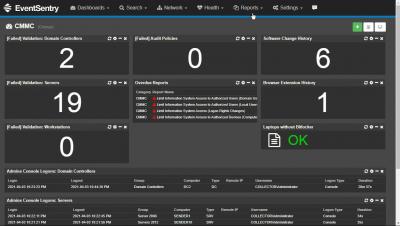
CMMC compliance with EventSentry
Using Google Workspace SSO with Teleport
https://goteleport.com/docs/enterprise/sso/ssh-gsuite/
0:00 Intro
0:45 Example Teleport with local login
1:12 Configure Google Workspace
3:35 Creating Service Account
5:00 Manage API Scope
6:36 Creating OIDC Connector in Teleport
10:04 tctl create gworkspace.yaml
10:13 Example Login with Google Button
Setting up Okta SSO with Teleport
0:00 Introduction
0:25 Okta Setup
0:42 Configuring Okta
3:24 Setting up Okta Groups
6:45 tctl create okta.yaml
7:16 Assigning Groups in Okta
7:41 SSO Debugging
8:50 Conclusion
Industrial IoT Needs to Catch Up to Consumer IoT
When it comes to cybersecurity, industrial IT—consisting mainly of operational technology (OT) and industrial control systems (ICS)—has failed to keep up with development in the enterprise IT world. That’s mostly because industries’ adoption of internet technology has been slower when compared with enterprises. It would take some time to close the gap, but concerted efforts have already been made to upgrade the security of industrial IT and improve the efficiency of OT and ICS.
3 Best Practices for Building Secure Container Images
Organizations are increasingly turning to containers to fuel their digital transformations. According to BMC, a 2019 survey found that more than 87% of respondents were running containers—up from 55% just two years earlier. Additionally, 90% of survey participants that were running applications in containers were doing so in production. That was up from 84% in 2018 and two-thirds of surveyed IT professionals a year before that.
Interview With Cyber Security Author Scott Steinburg
For our first specialist interview on the Logit.io blog, we’ve welcomed Scott Steinburg to share his thoughts on the current state of cybersecurity as well as the reasons behind writing his new book Cybersecurity: The Expert Guide. Scott is the creator of the popular Business Expert’s Guidebook series, host of video show Business Expert: Small Business Hints, Tips and Advice and CEO of high-tech consulting firm TechSavvy Global.
AWS IAM Privilege Escalation - Threat Research Release March 2021
The Splunk Threat Research Team recently developed an analytic story to help security operations center (SOC) analysts detect adversaries attempting to escalate their privileges and gain elevated access to Amazon Web Services (AWS) resources. In this blog, we’ll walk you through an AWS privilege escalation analytic story, demonstrate how we simulated these attacks using Atomic Red Team, collect and analyze the AWS cloudtrail logs, and highlight a few detections from the March 2021 releases.
From The Future CIO Report: For Most, Cyber Incident Response Remains a Challenge
With most organizations receiving over 100 threat alerts every day and a reduction of endpoint visibility due to the shift to remote work, the ability to quickly detect and confidently respond to cyber threats has become a difficult challenge for organizations to undertake on their own.