Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
AWS re:Invent 2022: How Neiman Marcus transitioned to developer-first security
At this year’s AWS re:Invent conference, Snyk’s VP of Product Marketing, Ravi Maira, spoke with Omar Peerzada, Cyber Security Architect at Neiman Marcus, about how his team transitioned from older security practices to a developer-first security strategy. Watch the full talk now, or keep reading for the highlights.
SBOMs and the Hunt for Software Supply Chain Vulnerabilities
That’s an excerpt from the fact sheet accompanying the May 2021 Executive Order on Improving the Nation’s Cybersecurity (EO). It refers to one of seven ambitious measures in the EO: shoring up security of that notorious playground for hackers, the software supply chain. Knowing that organizations lack visibility into the components that comprise their connected assets, bad actors can have a field day exploiting vulnerabilities to penetrate networks and take control.
CVE-2022-42475: Remote Code Execution vulnerability in Fortinet SSL VPN service
CVE-2022-3236: Official Patch Out Now for Remote Code Execution Vulnerability in Sophos Firewall
Finding Abusable Active Directory Permissions with BloodHound
BloodHound is a powerful tool that identifies vulnerabilities in Active Directory (AD). Cybercriminals abuse this tool to visualize chains of abusable Active Directory permissions that can enable them to gain elevated rights, including membership in the powerful Domain Admin group. This guide is designed to help penetration testers use BloodHound to identify these vulnerabilities first, so enterprises can thwart attacks.
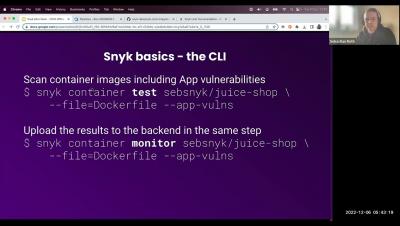
Customer Office Hours: CI/CD Best Practices
Finding Abusable Active Directory Permissions with BloodHound
BloodHound is a powerful tool that identifies vulnerabilities in Active Directory (AD). Cybercriminals abuse this tool to visualize chains of abusable Active Directory permissions that can enable them to gain elevated rights, including membership in the powerful Domain Admin group. This guide is designed to help penetration testers use BloodHound to identify these vulnerabilities first, so enterprises can thwart attacks.
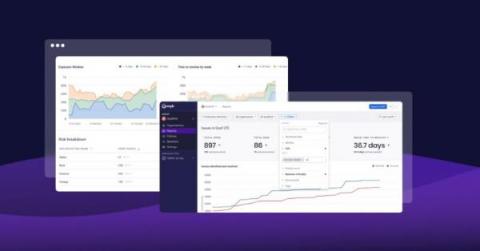
Using Snyk reporting for data-driven security
Last month, we announced the open beta of Snyk’s new and revamped reporting. Since then, we’ve been amazed at how creative our customers have been in leveraging these new capabilities to answer all sorts of different security questions. We’re not surprised. The new reporting was designed to provide easy access to data across the Snyk platform (including Snyk Code!), and to give customers flexible analysis tools to slice and dice data as they see fit.