Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
KeePass CVE-2023-32784: Detection of Processes Memory Dump
During May, a new vulnerability CVE-2023-32784 was discovered that affected KeePass. KeePass is a popular open source password manager which runs on Windows, Mac, or Linux. The vulnerability allows the extraction of the master key in cleartext from the memory of the process that was running. The master key will allow an attacker to access all the stored credentials. We strongly recommend updating to KeePass 2.54 to fix the vulnerability.
CVE-2023-27997: Critical Fortinet Fortigate SSL-VPN RCE Vulnerability
Snyk named a Leader, placed highest in Strategy category in The Forrester Wave: Software Composition Analysis (SCA), Q2 2023 report
We’re thrilled to announce that Snyk was named a Leader in The Forrester Wave™: Software Composition Analysis (SCA), Q2 2023 report! We believe this recognition — and the fact that we are ranked highest in the Strategy category out of all evaluated vendors — highlights the work we’ve done at Snyk to disrupt the industry with developer-centric application security solutions to help companies secure their software supply chain.
What is a QR Code? Its Usage, Vulnerability, Advantages, and Comeback Story - Part 1
This article helps you understand what a QR code is, how it works, the different types of QR codes, the rise in its usage, the risks involved, the advantages and disadvantages, and whether it is safe.
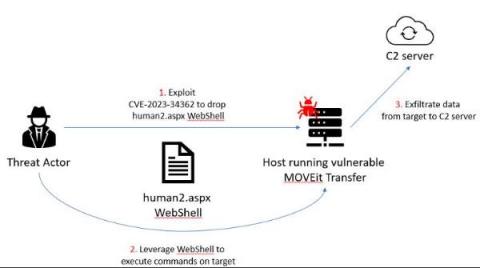
Mass Exploitation of MOVEit Transfer Critical Vulnerability - Recommended Mitigations and How Forescout Can Help
On May 31, Forescout Research – Vedere Labs uncovered a significant incident where threat actors exploited a critical zero-day vulnerability in the MOVEit Transfer software, which resulted in unauthorized access to and exfiltration of private data, as well as privilege escalation. MOVEit Transfer is a widely adopted managed file transfer (MFT) solution that enables organizations to securely exchange files with their business partners and customers.
Shielding Against the Most Recent Fortinet Vulnerability
During a red team assessment for a client, Charles Fol and Dany Bach from LEXFO, discovered a heap overflow bug in Fortigate’s SSL VPN that can be exploited to achieve remote code execution on Fortigate instances. This vulnerability is reachable without authentication, and can be used to execute arbitrary code on vulnerable systems, which could lead to a complete compromise of the system.