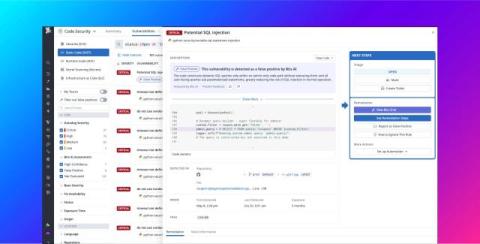
Fix SCA issues at scale in your terminal with Snyk Remediation Agent in the CLI
Snyk is now detecting six vulnerabilities for every one remediated. NIST reported a 33% increase in CVE submissions in Q1 2026. According to Gartner, the average time to patch a high/critical vulnerability is 55 days (Gartner, "How to Respond to the 2026-2027 Threat Landscape," 28 May 2026).