Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
URGENT: Analysis and Remediation Guidance to the Log4j Zero-Day RCE (CVE-2021-44228) Vulnerability
A previously unknown zero-day vulnerability in Log4j 2.x has been reported on December 9, 2021. If your organization deploys or uses Java applications or hardware running Log4j 2.x your organization is likely affected.
Detecting Exploitation of CVE-2021-44228 (log4j2) with Elastic Security
To understand how Elastic is currently assessing internal risk of this vulnerability in our products please see the advisory here.
Log Jammin'- Detecting Log4j 2 RCE Using Splunk
Authors and Contributors: As always, security at Splunk is a family business. Credit to authors and collaborators: Ryan Kovar, Shannon Davis, Marcus LaFerrera, John Stoner, James Brodsky, Dave Herrald, Audra Streetman, Johan Bjerke, Drew Church, Mick Baccio, Lily Lee, Tamara Chacon, Ryan Becwar. If you want just to see how to find detections for the Log4j 2 RCE, skip down to the “detections” sections.
What is Metasploit?
The Metasploit Framework is a Ruby-based, open-source framework that is used by information security professionals and cybercriminals to find, exploit, and validate system vulnerabilities. The framework consists of various exploitation tools and penetration testing tools. Information security teams most commonly use Metasploit for penetration testing (or “ethical hacking”) to identify and remediate any existing vulnerabilities across an organization’s networks.
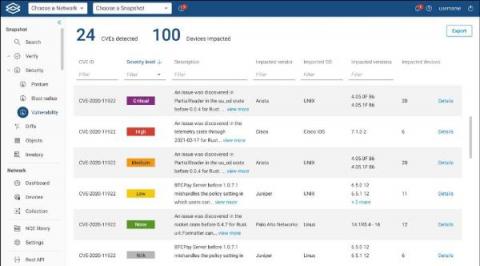
Of the nearly 165,000 known CVEs, which ones are putting your company at risk?
There are almost 165,000 known CVEs (Common Vulnerabilities and Exposures) listed in the NIST Database. In October of 2020, the NSA published a list of the 25 CVEs most likely to be exploited by Nation-State attackers in China; Checkpoint software found over 3 million attempts to penetrate networks or steal files using these known vulnerabilities.
How to Make Your Vulnerability Management Metrics Count
Software development organizations are investing more and more resources in their vulnerability management programs. According to Gartner’s forecast, in 2021 enterprise security spending was expected to break records and grow 12.4% to reach 150.4 billion. But how do organizations know if they’re spending their security resources wisely? The answer can only be found by crunching the numbers.
Redscan analysis of NIST NVD reveals record number of vulnerabilities in 2021
Malicious npm Packages Are After Your Discord Tokens - 17 New Packages Disclosed
The JFrog Security research team continuously monitors popular open source software (OSS) repositories with our automated tooling, and reports any vulnerabilities or malicious packages discovered to repository maintainers and the wider community. Most recently we disclosed 11 malicious packages in the PyPI repository, a discovery that shows attacks are getting more sophisticated in their approach.
Cybersecurity in 2022, Predictions for digital ecosystem facing more challenges and sophisticated threats
In 2020, I published an AT&T blog called “Top Cybersecurity Trends & Predictions for 2020’”. In the article I had forecasted that cybersecurity would become even more of a strategic priority for companies as the cost, sophistication, and lethality of breaches would continue to rise.