Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Trustwave's Action Response: Multiple Log4j Zero-Day Vulnerabilities
Dec. 29: Updated to cover three additional CVEs: CVE-2021-4104, CVE-2021-44832, and CVE-2021-42550 (in logback as opposed to log4j). Dec. 22: A joint Cybersecurity Advisory was issued by multiple national cybersecurity agencies providing mitigation guidance on addressing vulnerabilities in Apache’s Log4j software library: CVE-2021-44228 (known as “Log4Shell”), CVE-2021-45046, and CVE-2021-45105. Dec. 17: Please note the emergency directive from CISA on Log4j.
Press information: Crowdsource hacker first to find Zero-Day CVE-2021-43798 in Grafana
The vulnerability, dubbed CVE-2021-43798 impacted the Grafana dashboard, which is used by companies around the world to monitor and aggregate logs and other parameters from across their local or remote networks. The privately reported bug became a leaked zero-day but was first spotted by Detectify Crowdsource hacker Jordy Versmissen on December 2, after which Grafana was notified by Detectify about the bug.
How CrowdStrike Protects Customers from Threats Delivered via Log4Shell
Recent CrowdStrike Intelligence team findings regarding the Log4Shell (CVE-2021-44228, CVE-2021-45046) vulnerabilities indicate wide-ranging impact. CrowdStrike helps protect customers from threats delivered via this vulnerability using both machine learning and indicators of attack (IOAs).
CVE-2021-45046: New Log4j Vulnerability Discovered
Shortly after the Apache Software Foundation (ASF) released the bug fix for the vulnerability known as Log4Shell or LogJam (CVE-2021-44228), a new vulnerability was discovered in Log4j Java-based logging library, tracked as CVE-2021-45046. While Log4Shell had the maximum CVSS score of 10, this new vulnerability is rated as 3.7, affecting all versions of Log4j between 2.0-beta9 and 2.12.1, as well as between 2.13.0 and 2.15.0.
58% of Orgs Are Using a Vulnerable Version of Log4j
On December 9, 2021, a zero-day vulnerability in Log4j 2.x was discovered. This vulnerability is of great concern because if it’s successfully exploited, attackers are able to perform a RCE (Remote Code Execution) attack and compromise the affected server. Since we are a cloud-based Software Composition Analysis (SCA) provider, we have useful customer data that gives insight into the scope of the Log4j vulnerability.
Addressing Log4j2 Vulnerabilities: How Tripwire Can Help
On December 9th 2021, Apache published a zero-day vulnerability (CVE-2021-44228) for Apache Log4j being referred to as “Log4Shell.” This vulnerability has been classified as “Critical” with a CVSS score of 10, allowing for Remote Code Execution with system-level privileges. If you are currently working to identify instances of this vulnerability, Tripwire can help.
Log4j Log4Shell Vulnerability: All You Need To Know
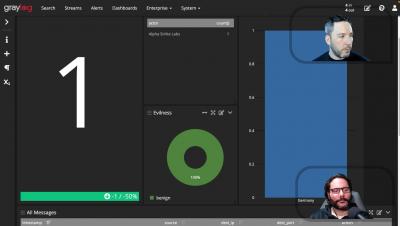
Detect Log4j RCE With Graylog GreyNoise
Log4Shell in a nutshell (for non-developers & non-Java developers)
If you’re in tech at all, you’ve likely heard of the Log4Shell exploit taking over the Intertubes. If you’re not a Java developer (or developer of any sort), you may be left scratching your head as to just what’s going on. This post is split into two parts: an explanation of Log4Shell for non-developers and an overview of the Log4Shell vulnerability for non-Java developers.