Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
5 ways to improve payment security in your business
Payment fraud is a huge problem for eCommerce and online retail businesses. Even among the world’s biggest companies, there are horror stories about payment security problems like credit card data theft and financial fraud: Cyberthreats like carding attacks are responsible for most modern large-scale data theft. Payment fraud losses cost companies more than $33 billion in 2021 — and this is expected to rise to more than $40 billion by 2027.
How Chatbot Automation Benefits Security Teams
When you hear the term “chatbot,” your mind may at first turn to things like robotic customer support services on retail websites – a relatively mundane use case for chatbots, and one that is probably hard to get excited about if you’re a security engineer. But, the fact is that chatbots can do much more than provide customer support.
Incident Response: Compare Options for Your Organization
Webinar: Back To Basics, All That You Need To Know About Securing Your Business - 28 July 2022
July Product Rollup: Web Redesign, Snapshot Recovery, and More
For this month’s product rollup, we’re excited to update you on our Egnyte UI redesign. We’ll also highlight improvements to search and snapshot-based ransomware recovery, as well as additions to our Quality App for Life Sciences and more.
KNOTWEED Assessment Summary
A Swift Kick in the Nuts and Bolts of Banking
The global financial services industry is undergoing a seismic shift and not enough people are truly aware of what this means. By November of this year, banks and other financial institutions must have in place a new process for payment systems that uses the ISO 20022 standard instead of SWIFT. This must be active by November and by 2025, all financial institutions will have to be compliant.
Keeper 101: Record History
Infrastructure as Code (IaC) - A Developer's Perspective
The organizations developed and deployed their IT infrastructure manually in the early days. The IT teams were responsible for the maintenance of hardware as well as software aspects of the infrastructure. Therefore, it is also applicable to the software development cycle. However, with technological advancement, many organizations have adopted cloud infrastructure for their business.
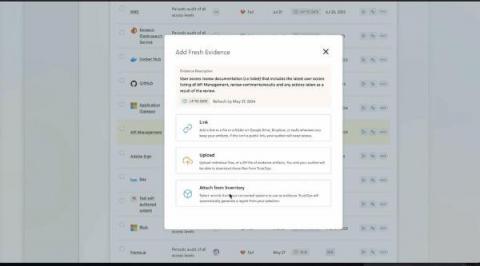
New In TrustOps: Evidence Automation with Smart Inventories
You want as much of your compliance program automated as possible, and collecting evidence to validate compliance controls always seems to take a lot of your team’s time. A considerable amount of control evidence involves providing accurate lists of artifacts to auditors — whether it’s workstations, tickets, alerts, or people. If only there were an easier way than having your teammates take screenshots and export lists from each of your internal systems.