Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Three Recent Examples of Why You Need to Know How Vulnerable Your Secrets Are
In today's digital landscape, the issue of compromised credentials has become a major concern. Discover how renowned companies like Microsoft, VMware, and Sourcegraph were recently confronted with the threats of secrets sprawling.
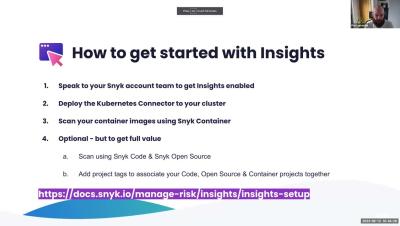
Office Hours: Insights - Focus on Top RIsks
Navigating Chaos: JFrog Security Essentials and Advanced Security
Security implications of cross-origin resource sharing (CORS) in Node.js
In modern web applications, cross-origin resource sharing (CORS) enables secure communication between applications hosted on different origins. Developers use CORS to access other applications’ services within their own. This approach eliminates the need to rewrite features from scratch, accelerating development time and improving the developer experience.
Demystifying NIST Vulnerability Management: A Comprehensive Guide
Protecting sensitive information and securing digital assets now require the use of cybersecurity. Organizations must employ proactive steps to spot and address vulnerabilities as cyber threats continue to become more complex and sophisticated. Vulnerability assessment is one such method, which is important in cybersecurity risk management.
The most common vulnerabilities in your external attack surface
Imagine your organization’s digital fortress – now picture a thousand hidden doors, each a potential entry point for cyber threats. In the world of cybersecurity, these doors are known as ‘external attack surface vulnerabilities’ and understanding them is the first step to locking them down. External attack surface vulnerabilities are the weak points of a company’s network that can potentially be exploited by malicious actors.
A guide to input validation with Spring Boot
If you're a developer working with Java, you likely know Spring Boot, the robust framework that streamlines the development of stand-alone, production-grade, Spring-based applications. One of the many features it offers is Bean Validation, which is a crucial aspect of any application to ensure data integrity and improve user experience.