Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Exploring The Foundations Of Cybersecurity Compliance
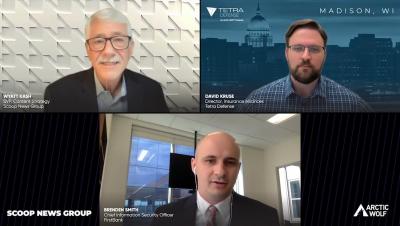
Guarding Against The Growing Business Of Cybercrime
Optimizing Security Postures Through Effective Security Operations
Replace Email Attachments with Links
Zeek on Windows
As we shared at ZeekWeek 2022 in October, we’re thrilled to announce emerging support for Zeek on Windows, thanks to an open-source contribution from Microsoft. Part of its integration of Zeek into its Defender for Endpoint security platform, this contribution provides fully-native build support for Windows platforms and opens up a range of future technical possibilities in this vast ecosystem.
How to verify and secure your Mastodon account
Mastodon, the free open source self-hosted federated social network platform, has been witnessing a surge of interest and new users due to the recent developments on Twitter — specifically that of verifying accounts. One of the interest areas driving users to Mastodon has been the ability to verify their account identity and convey a sense of authenticity for the account. This provides a way to help prevent spam accounts, bots, and other issues related to fake news.
Device Authority
How to Delete Your LastPass Account
Deleting your LastPass account is easy and is the last step to take after finding a great LastPass alternative. There are two different processes depending on whether or not you know your LastPass master password. Please follow the steps below to delete your LastPass account.
Cryptojacking Attacks See Growth Despite Weak Year for Cryptocurrency
2022 has seen a slowdown for the cryptocurrency ecosystem, as well as a decrease in demand for cryptocurrency-related activities like cryptomining. Even before the catastrophic implosion of the FTX cryptocurrency exchange, multiple market bubbles (from failed exchanges other than FTX) and events like Ethereum’s highly anticipated transition from proof of work to proof of stake have dampened enthusiasm for cryptocurrencies.
How to Overcome Access Governance Challenges in Multi-Cloud Environments
Identity governance, also known as access governance, is an integral part of any enterprise data protection and compliance framework. Seamless and timely access to required systems or resources can significantly increase employees’ productivity and performance. However, excessive privileges or unmonitored user access can often lead to internal and external cybersecurity threats, such as insider attacks, data breaches, and unauthorized access.