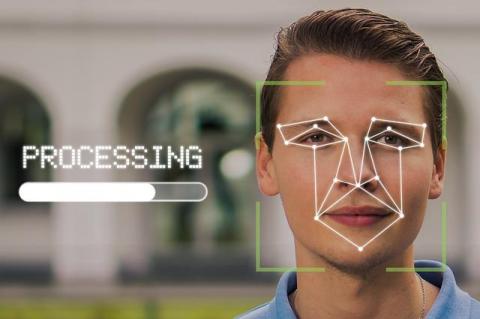
How to Use Facial Recognition for Face Search
The lives of modern people are becoming increasingly comfortable and productive, all thanks to the rapid advancement of innovative technologies. Nowadays, to communicate with acquaintances, make purchases, and pay for services, all you need to do is connect your device to the internet. Have you lost contact with an old acquaintance? This is easily remedied by Face search person by photo. The principle of search work is as simple as possible. To get the necessary information you should simply upload a photo to the search engine.