Essential Features to Look for in a VM Solution
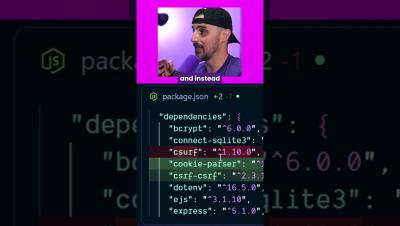
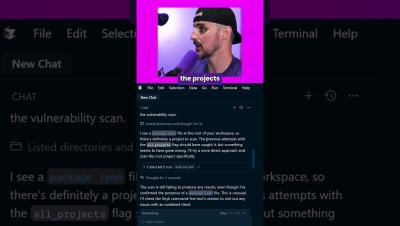
Your vulnerability management solution is the fuel that powers the rest of your strategic cybersecurity objectives. Put good in, get good out. That's why the vulnerability management tool you choose matters. And there are a lot of features that are necessary to protect a modern environment today that weren't on the list before. Done right, VM provides a stable foundation for cyber hygiene and regulatory compliance.