Hangin' with Haig: Conversations Beyond the Keyboard with Guest Simon Jones of Helping Rhinos
Overview: CyberResearch by UpGuard
UpGuard has launched an exciting new product called CyberResearch. This post summarizes the solution and its key features. CyberResearch is a suite of fully managed services, encompassing third-party risk and data leak detection. This world-first innovation is designed to further reduce the risk of data breaches while making it easier than ever before to scale your cybersecurity efforts.
XR Money Rebellion Planning Movement Vs Banks, Financial Institutions
Extinction Rebellion (XR) is a London-based environmental group aiming at disruptive and nonviolent civil resistance. Launching their first public campaign in October 2018, XR centers their motives on resisting structures that dismiss climate change and degradation of natural resources[1]. XR has been notable in eliciting mass arrest, a Ghandian tactic that garnered them press coverage, funding, and attention from government agencies and policy bodies.
Integrating With ServiceNow for a Single Source Of Truth
Network operations teams rely on highly specialized tools developed by individual vendors designed to address particular problems. The result? Most enterprises have 10+ Network Operations applications in place and they don’t talk to each other—which means that network operations engineers spend an exhaustive and unnecessary amount of time toggling between applications and sifting through information as they work to resolve tickets.
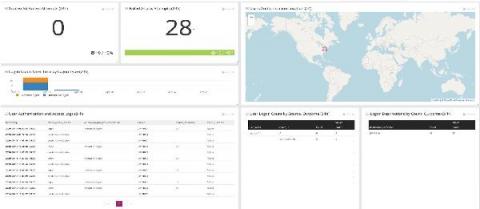
Monitoring Logs for Insider Threats During Turbulent Times
For logs and tracking insider threats, you need to start with the relevant data. In these turbulent times, IT teams leverage centralized log management solutions for making decisions. As the challenges change, the way you’re monitoring logs for insider threats needs to change too. Furloughs, workforce reductions, and business practice changes as part of the COVID stay-at-home mandates impacted IT teams.
Stories from the SOC - Propagating malware
While freeware does not have monetary cost, it may come at a price. There may be limitations to freeware such as infrequent updates, limited support and hidden malicious software. Some freeware programs may have added software packages that can include malicious software such as trojans, spyware, or adware. It’s important to have additional layers of defense to provide that your environment is protected.
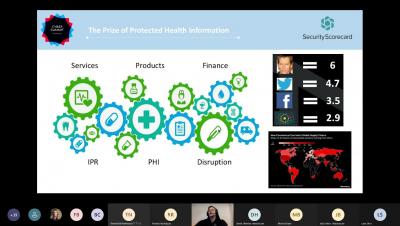
Third-Party Risk Management in Healthcare
Top 5 Most Powerful IoT Security Testing Tools
The network of interconnecting devices to exchange data popularly known as the Internet of Things is evolving rapidly in the fast-paced industry of technology. However, advancement in IoT has also taken a toll on security. IoT Systems strive to enhance productivity, efficiency, and flexibility but also invite uncalled risks to the network. IoT Security stands as the need of the hour for secure and holistic development.