Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
July 2023
FIPS 140-2: Validation VS Compliance
NIST established the crucial set of guidelines known as FIPS 140-2 to safeguard sensitive data, particularly for governmental organizations. It is to provide security and privacy when encrypting and decrypting data. The primary distinction between FIPS 140-2 validation and compliance is that. In contrast, validation involves determining if a system or product has been developed to comply with the standard’s requirements; compliance is putting those requirements into practice.
Peeping Through Windows (Logs): Using Sysmon & Event Codes for Threat Hunting
What is Active Roles? | One Identity
How to Implement Effective Compliance Testing
ATARC Publishes Cybersecurity Posture Guidance for State & Local Agencies
The Advanced Technology Academic Research Center (ATARC) published its intermediate level document providing guidance to state and local agencies using the Cybersecurity & Infrastructure Security Agency (CISA) Zero Trust Architecture (ZTA) model as a foundation. This document is a must-read for all state and local agencies, particularly those who are interested in pursuing any of the $1 billion in federal cybersecurity grant money over the next few years.
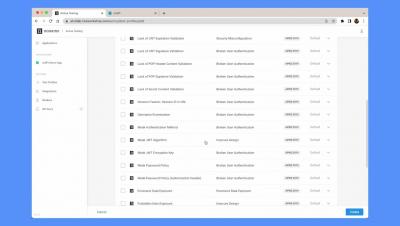
Noname Security Blocking Demo using AWS WAF
Active Testing v2 Demo
See it in action: Privacy-first generative AI with Elastic
Privacy-first generative AI with Elastic
Unlocking the Potential of UEBA With Logsign
In today's cybersecurity landscape, traditional security tools alone are inadequate in protecting organizations from advanced threats like data breaches, insider risks, and more. To effectively address these challenges, organizations require a comprehensive solution with UEBA (user and entity behavior analytics) capabilities. Let's discover the benefits of UEBA, and the unparalleled impact Logsign’s Unified Security Operations Platform has on UEBA.
What are Cloud Testing Tools?
Cloud testing tools are a set of software and hardware components that allow developers, testers, and IT professionals to test applications in the cloud. These tools give companies access to an array of cloud resources they can use for testing purposes. The cloud can provide a more cost-effective, agile, and scalable platform for testing applications compared to traditional on-premise systems.