Featured Post
The popularity of Large Language Models (LLMs) has prompted an unprecedented wave of interest and experimentation in AI and machine learning solutions. Far from simply using popular LLMs for sporadic background research and writing assistance, LLMs have now matured to the degree where particular solutions are being used within specific workflows to solve genuine business problems. Industries such as retail, education, technology, and manufacturing are using LLMs to create innovative business solutions, delivering the required tools to automate complex processes, enhance customer experiences, and obtain actionable insights from large datasets.
Featured Post
When an incident occurs, from an unfortunate car accident to damaged business equipment, policyholders rely on mobile applications and online portals that collect information, open claims, and process them through automated workflows. Behind the scenes, an insurer's APIs handle what amounts to a policyholder's life story in data.
|
By Stas Neyman
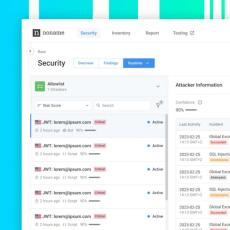
The latest Noname Security 3.32 update includes major enhancements to the getting started experience, in-app guides and tutorials, and a new way to view historical information about attackers.
Featured Post
With the move to hybrid working, the rapid adoption of cloud, increased use of mobile and IoT devices, combined with the ongoing drive to modernise and transform IT operations, the attack surface of every organisation has - and continues to - expand. Traditional boundaries have been blurred between businesses, suppliers, partners, customers, workers, and even home-life, with this ecosystem continuing to grow. Here, APIs are providing the connective tissue for modern applications and legacy infrastructure to co-exist. However, this means that the API attack surface is also rapidly expanding.
Featured Post
With the arrival of Large Language Models (LLMs) such as ChatGPT, BERT, Llama, and Granite, the operational dynamics within the enterprise sector have significantly changed. LLMs introduce unique efficiencies, paving the way for innovative business solutions. LLMs currently stand at the forefront of technological advancement, offering enterprises the tools to automate complex processes, enhance customer experiences, and obtain actionable insights from large datasets.
|
By Stas Neyman
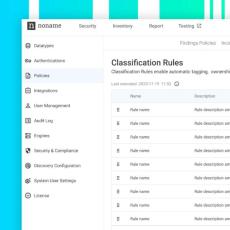
The latest Noname Security 3.31 update includes API classification rules that make managing API inventory easier and more efficient. It also features several UI enhancements to simplify the end-user experience with the Noname API Security platform.
|
By Andre Kerstens
Why is API security crucial for insurance companies? Consider what happens when disaster strikes, from an unfortunate car accident to damaged business equipment. Policyholders rely on mobile apps and online portals that collect information, open claims, and process them through automated workflows. Behind the scenes, an insurer’s APIs handle what amounts to a policyholder’s life story told in the form of data. These APIs exchange: This proximity to data is what makes APIs a significant risk.
|
By John Natale
Why have forty-four percent of enterprises been fined by regulators due to API security incidents? Regulators are beginning to see what attackers already know: exposed or misconfigured APIs are prevalent, easy to compromise, and often unprotected. Every time a customer, partner, or vendor engages with your business digitally, there’s an API behind the scenes facilitating a rapid exchange of data, often sensitive.
|
By Stas Neyman
The latest Noname Security 3.30 update includes a new feature that allows for convenient tracking of attacker IP addresses, as well as improved options for triggering workflows to resolve attacks faster. Additionally, the process of installing Noname Remote Engine on local Kubernetes clusters has been simplified.
|
By John Natale
Complying with data protection regulations isn’t easy, but it has traditionally involved dealing with familiar risks. For example, do your IT admins have the right amount of access to systems touching sensitive information? Review, remediate, report, and repeat. Compliance has been cumbersome, but workable. The problem is, today’s attack surface is nowhere near workable. And it’s evolving to include threats that most compliance programs aren’t yet accounting for.
|
By Noname Security
Business logic refers to the set of rules that govern the behavior of a business. At its core, business logic is used in making decisions based on what makes sense for your company. Despite these benefits, business logic doesn’t come without risk as vulnerabilities if your applications rely on business logic to function.
|
By Noname Security
Data exfiltration is the unauthorized transferring of data out of a secure environment, usually for malicious purposes. It’s improper exporting of data; a data breach that ends up with data in the wrong hands. One might say it’s a fancy word for stealing. Outsiders, employees, and contractors can exfiltrate data, but it is often difficult to detect until it’s too late.
|
By Noname Security
CSPM stands for Cloud Security Posture Management. It’s a security solution that helps organizations identify, assess, and remediate potential security risks or misconfigurations within their cloud infrastructure. CSPM tools provide continuous monitoring and analysis of cloud resources, ensuring adherence to best practices and compliance with security standards.
|
By Noname Security
API posture management is a part of IT and cybersecurity practice that seeks to ensure maximum protection of APIs. The specifics of API posture management vary by organization, as well as by the toolset used for its implementation.
|
By Noname Security
API Security requires Machine Learning because it is a superhuman problem to solve. With the strong partnership between Noname Security and IBM, you can protect all of your APIs and leverage the game-changing capabilities of AI/ML solutions like Watsonx to drive a faster and more secure API security practice. Learn how you can start accelerating your API security today.
|
By Noname Security
A business continuity plan, or BCP, is a collection of procedures organizations use for maintaining their operations during times of crisis. It is a cross-functional guide that includes communication and collaboration plans, as well as back-up procedures. A well-developed BCP can help organizations avoid disruptions when dealing with unexpected outages.
|
By Noname Security
Defense in Depth (DiD) is a cybersecurity strategy that involves deploying multiple types of defensive layers. The underlying theory holds that digital assets will be better protected if a malicious actor has to penetrate more than one barrier to succeed in an attack.
|
By Noname Security
PSIRT stands for Product Security Incident Response Team. It’s a team within an organization that handles and responds to security incidents related to its products or services. The main purpose of a PSIRT is to identify, assess, prioritize, and respond to vulnerabilities or threats that may impact the security of the organization’s offerings.
|
By Noname Security
Identity and Access Management (IAM) provides a critical, foundational element of cybersecurity, which is the tracking of who users are and what each user is entitled to do in a digital environment. People tend to think of IAM as a solution, but it’s actually a framework that serves as the basis for solutions, along with a range of work processes.
|
By Noname Security
Simple Object Access Protocol, better known as SOAP, is a standards-based messaging protocol specification. Introduced in 1998, SOAP and a handful of other web standards became the foundation for a generation of enterprise technologies. SOAP APIs are especially handy when it’s necessary for a server and client to exchange data in a structured format, as SOAP messages are built in extensible markup language (XML).
|
By Noname Security
Enterprises manage thousands of APIs, many of which are not routed through a proxy such as an API Gateway or WAF. Which means they are not monitored, rarely audited, and are most vulnerable to mistakes, misfortune, and mischief. This has left enterprise security teams to play catch-up when it comes to API security. In fact, Gartner predicts that 'by 2025, less than 50% of enterprise APIs will be managed as explosive growth in APIs surpasses the capabilities of API management tools.' Below are some of the key reasons that explain the proliferation of APIs and why many of them are left unsecure.
|
By Noname Security
The OWASP Top 10 is a standard awareness document and is the closest approximation of a set of rules for how to build secure applications that the development and web application security community has. We created this ebook to provide an overview of the OWASP top 10 API security vulnerabilities, and the methodologies used to mitigate them.
|
By Noname Security
With the number of APIs skyrocketing, companies are facing increasing challenges when it comes to security. Oftentimes, either there aren't enough security personnel who know how to test APIs, the number of APIs are growing faster than the security team can keep up with, or the existing security tools lack adequate coverage. Any one of these three scenarios can spell disaster for your environment. However, there is one overlooked aspect that could also weaken your API security posture if not addressed - and that's testing APIs early in the development process.
|
By Noname Security
Today, businesses rely on APIs more than ever before. Gartner estimates that API calls represent 83% of all web traffic. Given the increased reliance on APIs, their importance to digital businesses, and the rising level of sophistication of hackers looking to compromise those APIs, organizations need a proven strategy for API security.
|
By Noname Security
Application Programming Interfaces (APIs) are among the foundations of modern digital business, powering the logistics of delivering digital products to partners and customers. However, Security experts have warned about numerous security risks of APIs for years. But until quite recently, many organizations still believed that their API-related risks can be sufficiently addressed by existing security tools like web application firewalls (WAFs).
- June 2024 (3)
- May 2024 (6)
- April 2024 (2)
- March 2024 (11)
- February 2024 (7)
- January 2024 (5)
- December 2023 (9)
- November 2023 (7)
- October 2023 (7)
- September 2023 (3)
- August 2023 (14)
- July 2023 (11)
- June 2023 (14)
- May 2023 (4)
- April 2023 (11)
- March 2023 (10)
- February 2023 (9)
- January 2023 (3)
- December 2022 (7)
- November 2022 (7)
- October 2022 (14)
- September 2022 (9)
- August 2022 (2)
- July 2022 (1)
- May 2022 (1)
- April 2022 (1)
- March 2022 (2)
Proactively secure your environment from API security vulnerabilities, misconfigurations, and design flaws. Protect APIs from attacks in real-time with automated detection and response.
The Complete, Proactive API Security Platform:
- Discover all of your APIs: Find and inventory every type of API, including HTTP, RESTful, GraphQL, SOAP, XML-RPC, JSON-RPC, and gRPC. Discover legacy and rogue APIs not managed by an API gateway, and catalog data type classifications for all APIs.
- Detect API threats and prevent attacks: API security risks and issues are not all discovered in source code alone. Monitor real-time traffic using AI and ML-based detection to uncover data leakage, data tampering, data policy violations, suspicious behavior, and API security attacks.
- Test API security before production: Most applications have security testing before going into production. Most APIs do not. Increase API security assurance with greater speed, efficacy, and scale with integrated API-specific testing for CI/CD pipelines.
The Complete API Security Platform.