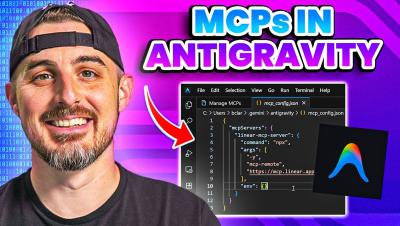
How to Add MCP Servers to Google's Antigravity IDE
In this video, I walk you step by step through the process of adding MCP servers to Google’s Antigravity. You’ll learn how they integrate with Antigravity and how to configure them correctly so everything runs smoothly.