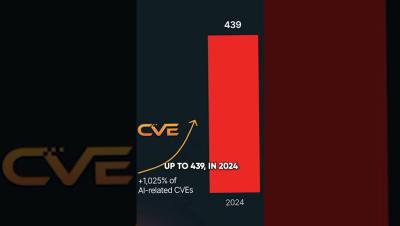
AI Security = API Security: 10x Surge in AI-Related CVEs #AIExploits #APIAttacks #SecureAI
AI-driven applications rely on APIs, making them a prime target for attackers. In 2024, AI-related CVEs increased 10x, with 98.6% of vulnerabilities linked to APIs. As AI agents interact with systems via APIs, security risks grow. Learn why securing AI means securing APIs.