Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Best practices to ensure data security while working remotely
Coronavirus has disrupted daily life for so many around the world in a shockingly short span of time. Lifestyles have shifted. A new normal, albeit a panic-stricken one, has set in. One-third of the global population is under lockdown to slow the spread of coronavirus. Many organizations have adopted temporary work-from-home measures to keep themselves up and running.
CyberGRX vs RiskRecon Comparison
Outsourcing, digitization, and globalization have led to new products and services, increased specialization, lower costs, and better access for customers and organizations alike. They've also introduced significant cyber risk, particularly the risk of unintended data exposure in the form of a data breach or data leak. In fact, a recent study by the Ponemon Institute and IBM put the average cost of a data breach at $3.92 million.
Whistic vs UpGuard Comparison
Outsourcing, digitization, and globalization have created new products and services, increased specialization, lowered costs, and improved access for customers and organizations alike. The downside is they've introduced cyber risk. Particularly the risk of data breaches and data leaks. In fact, a recent study by the Ponemon Institute and IBM put the average cost of a data breach at $3.92 million.
Zoom promises to improve its security and privacy as usage (and concern) soars
What’s happened? Well, Coronavirus 2019 (COVID-19) happened. Okay, smart alec. I know about that. What else is going on? Well, because so many people are (wisely) staying at home, they’re using videoconferencing and chat technology like Zoom to keep in touch with friends, family and colleagues. In fact, Zoom says that daily usage has soared from approximately 10 million daily meeting participants in December 2019 to over 200 million today. Zoom must be pleased. I’m sure they are.
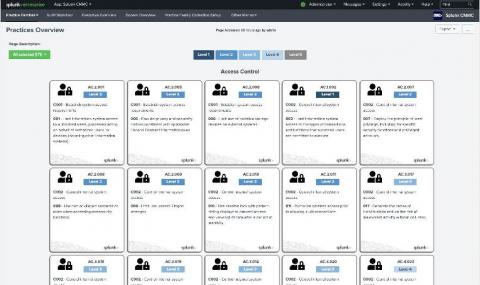
Recapping the Splunk for CMMC Solution Launch
On Wednesday, March 25th, we launched our Splunk for CMMC Solution with a webinar presentation to a diverse set of defense industrial base (DIB) participants and partners. As I discussed during the launch event, the Splunk for CMMC Solution provides significant out-of-the-box capabilities to accelerate organizations’ journeys to meet, monitor, track, and mature the cybersecurity practices required by the Cybersecurity Maturity Model Certification (CMMC).
The foundation of a Zero Trust architecture
Organizations have placed a lot of time, effort and capital spend on security initiatives in an effort to prevent security breaches and data loss. Even the most advanced “next generation” application layer firewalls filtering malicious traffic at the network perimeter has only revealed equal if not greater threats within.
Top 12 tips every pentester should know
In 2020, both big and small companies alike are embracing pen-testing as a solution to ensure the quality and availability of their mission-critical communication systems and data storage. Detectify Crowdsource is our private bug bounty community that’s powering our automated web security scanners to protect 1000s of security teams.
Webinar on Key to Effective Cloud Security in 2020
The rise in cyberattacks surrounding the COVID-19 pandemic
Fear, uncertainty, and doubt are powerful emotions, and time and again, hackers attempt to leverage these for their own gain. As the coronavirus develops into a worldwide pandemic, hackers are taking advantage of the fear many of us feel to spread malware. We’re seeing an abundance of coronavirus-themed phishing, business email compromise (BEC), malware, and ransomware attacks targeting different industries, especially in the health sector.
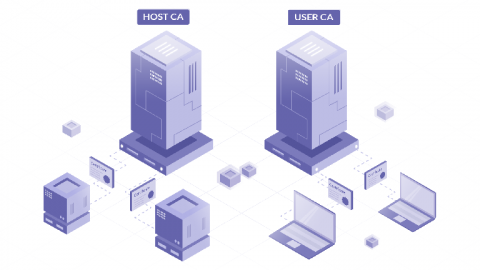
How to SSH Properly
There’s no denying that SSH is the de facto tool for *nix server administration. It’s far from perfect, but it was designed with security in mind and there’s been a huge amount of tooling written over the years to make it easier to use. In addition, many popular products and just about every server deployment system integrates with SSH somehow.