Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
We're All Remote Here: Videoconferencing Securely
The current pandemic has certainly shown the utility of electronic collaboration tools such as videoconferencing platforms. Once an expensive perk of solely enterprise companies, the video call is now used not only for executives remotely attending board meetings but also for the following... At the moment, it’s important for public health that everyone stays distant from one another.
Uncovering Bots in eCommerce Part One: Carding
No one wants to be a victim of payment card fraud, yet more of us are falling foul to the myriad of techniques used by hackers to steal payment card information and use it for their own gain. To mitigate this malicious activity, it is vital that eCommerce sites apply security measures that protect consumers and sellers alike from carding and other major bot threats.
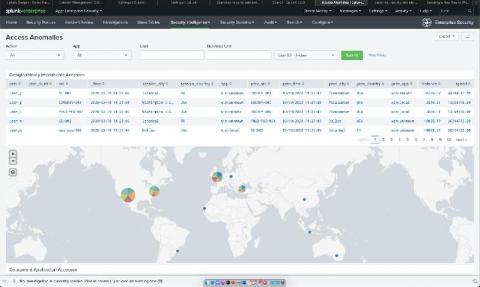
Between Two Alerts: Easy VPN Security Monitoring with Splunk Enterprise Security
Welcome to the new world, my friends. Now that working from home is our new reality, we've found that many of our customers are taking a much closer look at the technology that binds us all together and allows us to access corporate resources: the humble VPN. In the spirit of enablement, I’ve put together a quick list of dashboards that can help add that extra bit of visibility for our faithful Splunk Enterprise Security customers.
9 Reasons to hire an InfoSec candidate without experience: Focus on skillset vs. experience
This blog was written by an independent guest blogger. $37-$145k jobs for InfoSec specialists without experience. Hiring immediately. This is what a simple internet search has to offer for people looking to get entry-level jobs in Information security (InfoSec), or cybersecurity. It seems like a good deal, considering that the requirements for candidates are much lower compared to many other jobs.
Appknox Webinar: Effective Cloud Security Episode - 1
PCI Compliance for Containers and Kubernetes
In this blog, we will cover the various requirements you need to meet to achieve PCI compliance, as well as how Sysdig Secure can help you continuously validate PCI compliance for containers and Kubernetes. Learn how to meet PCI Compliance Requirements for Container and Kubernetes Environments!
BitSight vs CyberGRX Comparison
Due to increased outsourcing, digitization, and globalization, vendor risk management has become a top concern for CISOs and senior management around the world. These three forces have led to better products and services for consumers while giving organizations the ability to focus on core competencies while reducing costs and accessing new, global markets. That's the good news, the bad news is these same forces introduce significant cyber risk, particularly data breaches and data leaks.
SecurityScorecard vs CyberGRX Comparison
Outsourcing, digitization, and globalization have made vendor risk management a top priority for CISOs and senior management alike. These forces have led to innovative products and services, increased specialization, lower costs, and increased access for customers and organizations alike. However, they've also introduced significant cyber risk, particularly the risk of unintended data exposure in the form of a data breach or data leak.
The Future is Hybrid:Key Considerations for Cloud and DevOps
The MITRE ATT&CK Framework: Execution
Of all the tactics that an adversary will take on in their campaign, none will be more widely abused than, Execution (https://attack.mitre.org/wiki/Execution). When taking into consideration off-the-shelf malware, traditional ransomware, or state of the art advanced persistent threat actors, all of them have execution in common. There’s a great quote from Alissa Torres which says, “Malware can hide, but it must run.”