Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Elastic Security Overview
"PlugWalkJoe" indicted for $784K SIM swap cryptocurrency theft
The U.S. Department of Justice charged a British man for his alleged role in stealing $784,000 worth of cryptocurrency using SIM swap attacks. According to the unsealed indictment, Joseph James O’Connor – also known as “PlugWalkJoe” – conspired with others to steal approximately $784,000 worth of cryptocurrency from a Manhattan-based cryptocurrency company.
How To Transfer Point Cloud Data Faster From the Jobsite
Which is staler: 14-day-old bread or your point cloud data? Affordable, reality-capture technologies are rapidly changing how AEC firms conceive of, design, and build structures today. Companies are using laser scanners, 360-degree cameras, drones, smartphones, and more to capture high-fidelity data that details every dimension throughout a project. Stakeholders can then use that data to collaboratively visualize, plan, build, adjust, and complete projects faster and more accurately.
Secure & Manage Office 365 with PowerShell - The CIS Approach
Office 365 is central to your business needs and business continuity. However, it exposes a large (maybe even the largest) risk surface in your organisation. It is, therefore, crucial to secure it enough to mitigate this ever-present and continuous risk but keep it open enough to ensure as fluid a business as possible. Getting this balance right is difficult, and it can be hard to know where to start. Adopting a common security standard can be a great place.
Detecting IcedID... Could It Be A Trickbot Copycat?
IcedID is a banking trojan, it is designed to be stealthy and built to collect financial information. IcedID harvests user credentials and banking sessions to commit financial crimes, including carding, money laundering, and transferring of funds to foreign financial institutions. In recent research published by Splunk Threat Research Team (STRT) the inclusion of cryptocurrency exchange information was also included by Trickbot in the web inject code.
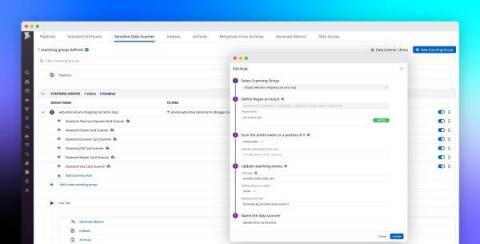
Build a modern data compliance strategy with Datadog's Sensitive Data Scanner
Within distributed applications, data moves across many loosely connected endpoints, microservices, and teams, making it difficult to know when services are storing—or inadvertently leaking—sensitive data. This is especially true for governance, risk management, and compliance (GRC) or other security teams working for enterprises in highly regulated industries, such as healthcare, banking, insurance, and financial services.
What is Compliance Management and Why Is It Important?
Every business has a set of rules and regulations that it must uphold. To maintain compliance, businesses must adhere to the regulations and laws specific to their industry. The problem is, these regulations are constantly changing, and failure to stay up-to-date can lead to serious financial strains and damage to company reputation. Let’s explore how effective compliance management can ensure the continuity and security of your organization.
Reversing a binary using GDB: tutorial for Reverse Engineers
Reversing binaries is an essential skill if you want to pursue a career as exploit developer, reverse engineer or programming. The GNU Project debugger is a widely used debugger for debugging C and C++ applications on UNIX systems. A debugger is a developer's best friend to figure out software bugs and issues. This tutorial intends to be beneficial to all developers who want to create reliable and fault-free software.
What is OWASP Mobile Security Testing Guide (MSTG)?
With millions of apps being released every day and ever-changing feature additions, it is more important than ever for enterprises to focus on security to prevent data breaches. According to Checkpoint, in 2020, 97 per cent of enterprises were confronted with mobile threats employing a variety of attack vectors. What is Mobile Security Testing Guide (MSTG)? The MSTG is a comprehensive manual for mobile app security testing.