Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
JavaScript type confusion: Bypassed input validation (and how to remediate)
In a previous blog post, we showed how type manipulation (or type confusion) can be used to escape template sandboxes, leading to cross-site scripting (XSS) or code injection vulnerabilities. One of the main goals for this research was to explore (in the JavaScript ecosystem) how and if it is possible to bypass some security fixes or input validations with a type confusion attack (i.e by providing an unexpected input type).
How and when to use Docker labels / OCI container annotations
Most container images are built using Dockerfiles which contain combinations of instructions like FROM, RUN, COPY, ENTRYPOINT, etc. to build the layers of an OCI-compliant image. One instruction that is used surprisingly rarely, though, is LABEL. In this post, we’ll dig into labels (“annotations” in the OCI Image Specification) what they are, some standardized uses as well as some practices you can use to enhance your container security posture.
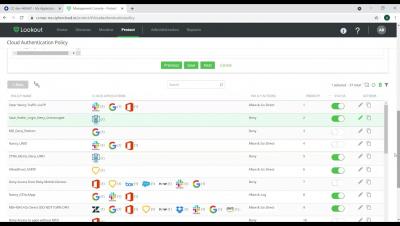
Lookout ZTNA - Setting up an access policy for unmanaged devices
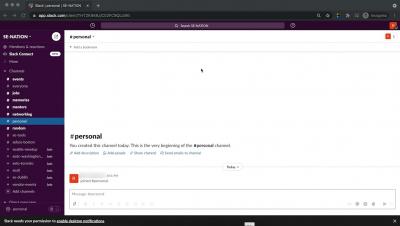
Lookout CASB - Preventing Sensitive Data Leakage to Personal Channels in Slack
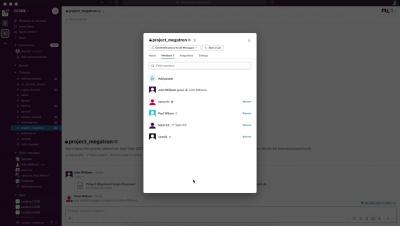
Lookout CASB - Secure Collaboration and Compliant Sharing of Content in Slack
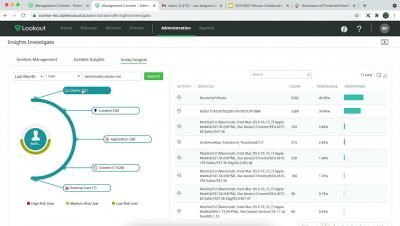
Lookout CASB provides enhanced visibility into activities in Slack
Lookout CASB Protects Sensitive Data in Slack by Masking data and Watermarking
Lookout Protects Against Mobile Phishing Threats
Zero Trust? Don't Forget Your Mobile Fleet
CIS Control 11: Data Recovery
Data loss can be a consequence of a variety of factors from malicious ransomware to hardware failures and even natural disasters. Regardless of the reason for data loss, we need to be able to restore our data. A data recovery plan begins with prioritizing our data, protecting it while it is being stored, and having a plan to recover data.