Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What is a Right-to-Left Override Attack?
The right-to-left override attack may be unassuming but incredibly malicious. Most people have heard about phishing attacks, but they think that opening a file with the ".txt" extension is harmless.
How to Upgrade Graylog In Docker
Key takeaways from the U.S. executive order on cybersecurity
On May 12, 2021, President Biden signed an executive order calling on federal agencies to improve their cybersecurity practices. Following the recent SolarWinds and Colonial Pipeline attacks, it is clear that security incidents can severely impact the economy and civilians' day-to-day lives and that cybersecurity needs to be a high-priority issue. We encourage you to read the full executive order.
Setting the cyberscene: Leading with a security first mindset
Our current global landscape is testing resiliency. As organizations continue to shift to a remote work business model, the rush to digitally transform has created new and heightened cyber risk concerns. Protecting these digital connections needs to stay top of mind for leaders looking to help their organizations adapt to these changes while continuing to innovate. In this blog, we will look to set the cyberscene and focus on a security first mindset.
OPA, Styra and Terraform: protect your cloud investment
The shift to cloud-native has transformed the way organizations do business, keep up with the competition and meet the demands of customer expectations. From the infrastructure that maintains IT operations to the applications that supply customers with the ability to interact with their data, the velocity in which DevOps teams have to deliver these services has significantly increased, leaving little to no room for error.
How Snyk is normalizing authentication strategies with Gloo Edge
Snyk supports multiple authentication (authN) strategies on its APIs. Historically, API keys have been the primary form of authN, but more recently we introduced support for authN using signed JWTs produced as a result of an OAuth integration. This is currently in use by both our AWS CodePipeline and Bitbucket integrations. In the beginning, Snyk began with a hub and spoke architecture with a central monolith making authN decisions.
Are You Prepared for the Surge in Ransomware?
Incidents of ransomware have been increasing and evolving steadily for years as financially motivated adversaries shift tactics when one is no longer profitable. Unfortunately, many organizations haven’t been able to adapt their security operations to keep up. Back in 2019, 60% of organizations told ESG that they experienced a ransomware attack that year, with 29% reporting that attacks happened at least on a weekly basis.
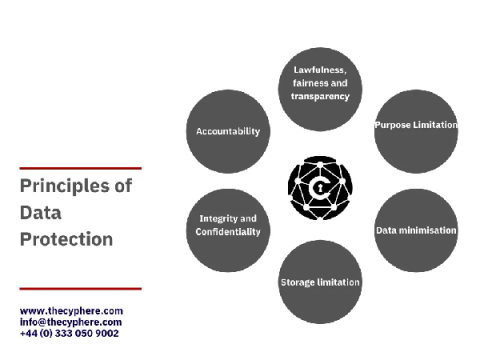
The 8 principles of The Data Protection Act & GDPR
The Data Protection Act 2018 is the legislation enforced by the Information Commissioner’s Office (ICO), UK, to protect personal data processing and data stored on the computer, digital media, or paper filing systems.
OWASP Mobile Top 10 Security Vulnerabilities and Attack Prevention
Far from the days of just phone calls and text messages, mobile apps have captured our attention with efficient experiences that keep us connected to friends, family members, coworkers. It’s all at your fingertips via these amazing apps- anywhere in the world! This blog post takes you through the OWASP mobile top 10 security risks, attack scenarios from OWASP and risk remediations that help cybercriminals get their hands on sensitive data.