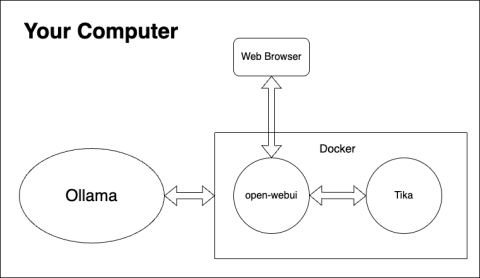
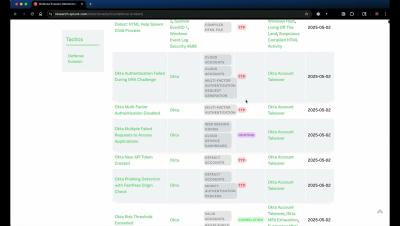
Empowering your LLMs: Unlocking cybersecurity queries with Open WebUI knowledge bases
In the rapidly evolving landscape of large language models (LLMs), the ability to access and synthesize vast amounts of information is paramount. While LLMs excel at generating creative text and understanding complex prompts, their knowledge is often limited to the data used during their training. This is where knowledge bases (a.k.a.