Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
RBAC and ABAC with AWS IAM
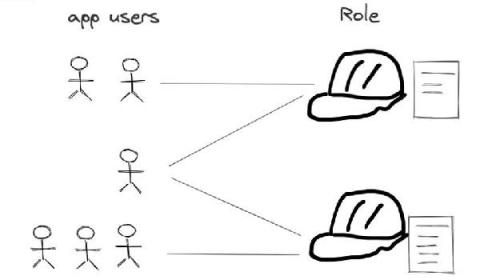
This is a guest blog post from Shuo Yang in his blog series “Transitioning to Programming the Cloud”, as a part of our blog posts focusing on Identity, Security and Access. We talked about how AWS CIP, STS and IAM can serve as the foundation of application authorization in our last post, i.e., how the application gets the temporary credential representing a specific role (i.e.
Critical Data Breach Stats for Australian Businesses in 2021
If you're an Australian business reading this, there's a 30% chance you will suffer a data breach. Such cutthroat statistics, as uncomfortable as they are to read, are important to be aware of if you want to avoid becoming one. To help you achieve a data-driven approach to cybersecurity, we've aggregated some of the most critical data breach stats for Australian businesses. This list also includes global data breach statistics that could be a window into Australia's future modified threat landscape.
The Impact Of Mergers And Acquisitions
The Current State of Ransomware: 2021 Edition
Cloud Security Best Practices: Four Tips for Moving Security Technologies to the Cloud
In my previous post, I discussed cloud-computing security challenges identified in our new report, Beyond Cloud Adoption: How to Embrace the Cloud for Security and Business Benefits. Based on a survey conducted by Enterprise Strategy Group (ESG), the report found that while cloud computing does initially introduce security challenges and increased complexity, it’s worth it in the end. That said, CISOs need to strategically invest time and resources to achieve better security outcomes.
Five Questions Your Organization Must Ask to Prepare For a Ransomware Attack
Since last week, I’ve been speaking with Splunk customers and our own team about the cyberattacks impacting the Kaseya software platform. While Splunk was not impacted by the ransomware attack, as a security leader we want to help the industry by providing tools, guidance and support. It’s critical that we work together as a community to counter cybersecurity threats and share information about events like these.
What is CREST penetration testing and why is it important to use a CREST-approved provider?
Trusting the effectiveness of your IT security controls is crucial to mitigate risks and malicious access to your systems and the information they store. Penetration testing with a CREST-Approved provider is one of the most effective methods to gain assurance of your IT security. Initiating a penetration test will give you the ability to develop (or enhance an existing) security strategy and remediate your vulnerabilities.
4 Reasons Traditional Security Automation Strategies Fail
For many businesses today, security automation is something of a paradox. It’s no secret that automation is important, and a large number of businesses have invested in security automation solutions. Yet the never-ending stream of headlines about major cybersecurity attacks suggests that, for most of these companies, security automation doesn’t end up delivering the intended results.