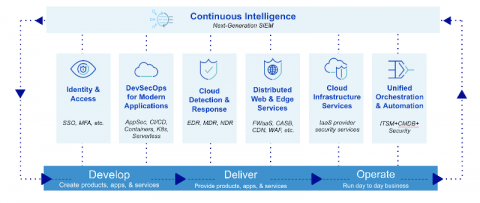
A New Framework for Modern Security
Veracode Streamlines AppSec Workflows for Developerswith New GitHub Action
Detecting & Preventing Ransomware Through Log Management
As companies responded to the COVID-19 pandemic with remote work, cybercriminals increased their social engineering and ransomware attack methodologies. Ransomware, malicious code that automatically downloads to a user’s device and locks it from further use, has been rampant since the beginning of March 2020. According to a 2020 report by Bitdefender, ransomware attacks increased by seven times when compared year-over-year to 2019.
SIEM Alerts Best Practices
Security Information and Event Management (SIEM) tools play a vital role in helping your organization in discovering threats and analyzing security incidents. Logsign’s internal team continuously makes correlation rules and alerts so that your team’s workload is minimized. In our previous posts, we discussed generating important reports and deriving maximum possible benefits from use cases. In this article, we will be discussing SIEM alerts best practices.
30 Ransomware Prevention Tips
Dealing with the aftermath of ransomware attacks is like Russian roulette. Submitting the ransom might seem like it’s the sole option for recovering locked data. But paying the ransom doesn’t mean that your organization will get its affected data back. Let’s not forget that ransomware also continues to evolve as a threat category.
Zerologon: Tripwire Industrial Visibility Threat Definition Update Released
Today, we released a Threat Definition Update bundle for our Tripwire Industrial Visibility solution to aid in the detection of Zerologon. Otherwise known as CVE-2020-1472, Zerologon made news in the summer of 2020 when it received a CVSSv3 score of 10—the most critical rating of severity. Zerologon is a vulnerability that affects the cryptographic authentication mechanism used by the Microsoft Windows Netlogon Remote Protocol (MS-NRPC), a core authentication component of Active Directory.
Role of CERT IN in Cyber crime Prevention
Securing Cloud Environments: Staying on top of cloud configurations to prevent data leaks.
File Integrity Monitoring (FIM): Your Friendly Network Detective Control
Lateral movement is one of the most consequential types of network activity for which organizations need to be on the lookout. After arriving at the network, the attacker keeps ongoing access by essentially stirring through the compromised environment and obtaining increased privileges (known as “escalation of privileges”) using various tools and techniques. Attackers then use those privileges to move deeper into a network in search of treasured data and other value-based assets.