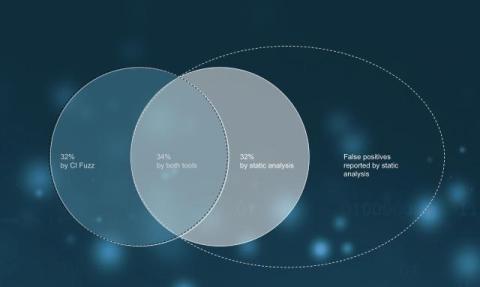
Automotive Supplier Finds 32% of Bugs Through Fuzz Testing
An automotive supplier employs static analysis and Code Intelligence's Fuzz Testing to assess software within a separate business unit. The project comprises 10 million lines of C code, adhering to Classic AUTOSAR standards.