The invisible threat: Machine identity sprawl and expired certificates
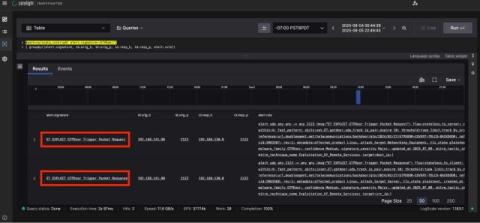
One unmanaged machine identity—whether a TLS certificate, SSH key, code signing certificate, or API secret—that’s all it takes to crash your website, halt transactions, and leave customers complaining about you in the comments. No one is immune. In fact, 83 percent of organizations have experienced a certificate-related outage in the past 24 months. Even tech giants recently made headlines after expired renewals triggered hours of downtime and millions in lost revenue.