Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
July 2023
A Guide to Vendor Relationship Management
8 Third-Party Risk Management Challenges + Solutions and Tips
How to Quantify the ROI of your GRC & Security Programs
GRC programs are often viewed as cost centers. But, they can in fact be profit drivers by contributing to sales acceleration, cost and time savings, and risk reduction. The real question is, how can you prove that to the board? TrustCloud teamed up with ISSA to discuss.
NIS2 Directive and cyber risk management
The NIS2 Directive, published in December 2022, sets out a series of measures for improving cyber risk management throughout the European Union. All EU member states must apply the Directive as part of national law by October 2024. By the same date, all applicable organizations must comply with the measures set out in NIS2.
What are Backdoor Attacks and How Can You Defend Against Them?
3 Takeaways: New SEC Cyber Risk Disclosure Rules
Yesterday the US Securities and Exchange Commission (SEC) voted 3-2 to issue long-awaited regulations that mandate uniform cyber incident disclosures for public companies. The SEC’s rulemaking progress has been lengthy and controversial, and cybersecurity experts and business advocates have been eagerly awaiting the release of the final rules after more than a year of public comment and lobbying from business and cyber experts.
Financial Services Cybersecurity: 4 Ways to Combat Modern Threats in this Vulnerable Sector
Leaders Embrace New SEC Cybersecurity Regulations
Common Types of Network Vulnerabilities for Businesses
How to Navigate the Maze of State Data Privacy Laws
How to Quantify the ROI of Your GRC & Security Programs: 3 Lessons Learned from Successful GRC Teams
5 Insights to Planning for a More Cybersecure World
SecurityScorecard recently joined the World Economic Forum’s Centre for Cybersecurity and UC Berkeley’s Center for Long-Term Cybersecurity (CLTC) for a private, invite-only workshop in Washington, DC alongside global leaders, CEOs, and CISOs to identify trends and insights that will most likely impact cybersecurity in the next decade of 2030 via future-focused scenarios with emerging cybersecurity challenges.
Cyber Security Behaviours: Bridging the Gap Between Awareness and Action
Webinar - Leveraging CRQ for Effective Board Level Decision Making
What Are the Types of Audit Evidence?
The collection and evaluation of audit evidence plays an important role in assessing an organization’s compliance with established standards. The American Institute of Certified Public Accountants (AICPA) serves as a guiding force, establishing methods that auditors should use to carry out their duties effectively. As auditors start their examination, they first collect and analyze various types of audit evidence, each serving as a piece of the puzzle that forms the auditor’s report.
Cyber Security Awareness Platform
New research reveals rapid remediation of MOVEit Transfer vulnerabilities
How I got Phished in my First 30 Minutes
What Happens When Someone Makes a Security Mistake?
Using Generative AI for Creating Phishing Sequences
How to Build Security Trust and Not Break It
Using the Right Security Behaviours at the Wrong Time
Understanding the Why, How, and Motivation of Phishing Incidents
How Do You Ensure a Culture of Empathy in an Organisation?
Mitigating Risks for Forex Brokers
Diligent and Bitsight Partner to Increase Board Confidence in Cyber Risk Oversight
Not all cybersecurity analytics are created equal: What CISOs should look for
Thrilling True Stories of State-Sponsored Cyber Espionage
What is Open Source Intel? Definition, Tools, & Solutions
In the digital age, an organization’s cybersecurity posture is as strong as its intelligence. Open-source intelligence (OSINT) has emerged as a vital tool for businesses, non-profit organizations, and governments alike to fend off cyber threats. This guide offers a deep dive into the realm of OSINT, detailing its importance, applications, challenges, and how SecurityScorecard’s cybersecurity assessment platform empowers organizations to utilize it effectively.
4 Tips for Effective Cyber Vigilance as Your Attack Surface Expands
Exposure Management: Best Practices for Getting Ahead of Cyber Risk
Choosing Cyber Risk Remediation Software in 2023 (Key Features)
New Feature: Risk Evaluation
Cyber Security Risk Modeling: What Is It And How Does It Benefit Your Organization?
Continuous Monitoring for Real Time Compliance
Analysis of CVE-2023-2868 Exploitation: Campaign Targeting U.S. Entities Using Barracuda Email Security Gateway
CVE-2023-2868, a vulnerability in the Barracuda ESG was announced on May 23. On June 15th, a report surfaced, attributing the exploitation of this vulnerability to a threat actor group tracked as UNC4841, which analysts believe is conducting espionage on behalf of the Chinese government. SecurityScorecard’s STRIKE Team consulted its datasets to identify possibly affected organizations.
Continuous Security Monitoring - 5 Key Components
Prioritizing Actionable Insights: The Power of Effective Continuous Control Monitoring Combined with CRQ
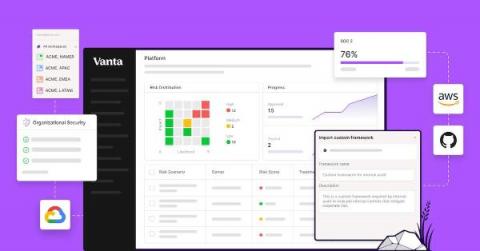
How Vanta combines automation & customization to supercharge your GRC program
As the industry’s first automated compliance platform, Vanta includes a wealth of pre-built content, which enables customers without existing compliance processes to quickly get up and running. But more mature organizations may already have a compliance program — from the processes they follow to the definitions of their compliance and security surface area — that is built to meet their unique compliance goals, auditor requirements, and tech stack.
Underwriting Cyber Risk Part 2: Metrics to Track Cyber Hygiene
What is Cyber Threat Hunting?
Cyber threat hunting is a proactive security strategy that involves searching for threats within a network before they can cause significant damage. Unlike traditional methods, which are reactive and wait for an alert before taking action, threat hunting seeks to actively identify and mitigate hidden threats that have evaded initial security measures. Threat hunting involves constant monitoring and data analysis to spot suspicious behavior that may indicate a cyber attack.
What Your Auditor Looks for in Your Risk Management Process
TrustCloud teamed up with Dansa D’Arata Soucia on our Risk Rodeo webinar, to discuss everything you need to know to wrangle up risks with confidence. Our panelists weighed in on the four things that auditors look for in risk management processes.
Cyber Security Awareness Training for Employees
What is cyber risk exposure and how can you manage it?
Is Cyber Insurance Worth It?
Simulated Phishing Training: Stay One Step Ahead
Creating A Successful Third Party Risk Management Program
How to Implement Effective Compliance Testing
TrustCloud Transforms Legacy GRC Programs with new API and AI-Powered Tools
Underwriting Cyber Risk Part 1: Focus on Cyber Hygiene
What's new in UpGuard // Cyber Vendor Risk Management Product Releases
What is Threat Intelligence?
Threat intelligence is one of the most potent weapons we have against digital hazards. Yet, many organizations remain uncertain about what it entails, how to apply it effectively, and what threat intelligence solution to choose. This lack of understanding could be detrimental as cyber threats continue to evolve, becoming more sophisticated and disruptive. So, what is threat intelligence, and how can it help bolster an organization’s security posture?
The Road to Continuous Compliance
What is Threat Intelligence in Cybersecurity?
The evolving threat landscape necessitates proactive approaches to identify, assess, and mitigate potential cyber security risks. Threat intelligence is one of the most potent weapons we have against digital hazards. Yet, many organizations remain uncertain about what it entails, how to apply it effectively, and what threat intelligence solution to choose. This lack of understanding could be detrimental as cyber threats continue to evolve, becoming more sophisticated and disruptive.
3 Key Metrics to Include in Your Cybersecurity Risk Analysis
Insiders' Guide to Advancing Your GRC or Cybersecurity Career
5 Things Everyone Needs to Know About GRC
Over the following years, the costs associated with cybercrime, projected at $10.5 trillion annually by 2025, will exceed the estimated worldwide cybersecurity spending—$267.3 billion annually by 2026. Leadership needs to change its perspective on managing cyber risks instead of just spending more money to match the losses incurred.