Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Top Cybersecurity Websites and Blogs of 2020
The information security landscape is constantly evolving, which is why it's so important to stay up to date with the latest trends, threats, and advancements. Given that a Google search for cybersecurity websites produces millions of results, we thought we thought we'd compile a list of the best. Adam Shostack & friends is a group blog on security, liberty, privacy, and economics.
Veriato Vision Intro and Demo
Netwrix Data Remediation Workflows - Overview
Netwrix Data Classification - Overview
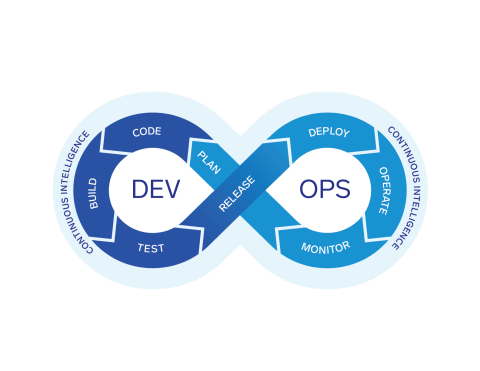
Ask the Experts: Lessons Learned from Cloud & DevOps
The MITRE ATT&CK Framework: Command and Control
Most malware these days has some level of Command and Control. This can be to exfiltrate data, tell the malware what instructions to execute next, or download encryption keys in the case of ransomware. In each case of command and control, the attacker is accessing the network from a remote location. Having insight into what is happening on the network is going to be crucial in addressing these techniques.
How Does Identity-Based Encryption Work?
With the help of breath taking technological advancements, the majority of our communications are conducted online. That is why encryption techniques are more important than ever. Keep reading to learn more about encryption techniques and identity based encryption.
A guide to penetration testing for compliance
In many cases, penetration testing – a type of ethical hacking engagement designed to identify and address security vulnerabilities in networks, systems and applications – is required. Sometimes this requirement is specified directly, while in other cases it is implied by a need to build audit or assessment processes to mitigate cyber risk. This blog identifies some of the most common pen testing standards and regulations and provides guidance about the type of testing required.
What Is Third-Party Risk Management?
Third-party risk management (TPRM) is the process of analyzing and minimizing risks associated with outsourcing to third-party vendors or service providers. This is commonly known as third-party risk or vendor risk and can include financial, environmental, reputational, and security risks due to a vendor's access to intellectual property, sensitive data, personally identifiable information (PII), and protected health information (PHI).