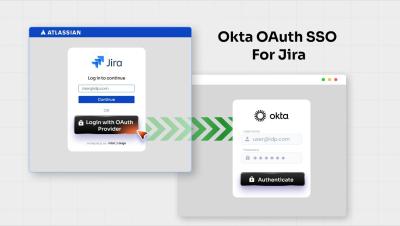
User management, MFA, SSO, and weekly summaries are live
We’ve got a boatload of features to show off this week. We knocked out some of the most common requests, user management, single-sign on, and my personal favorite: the weekly email summary.