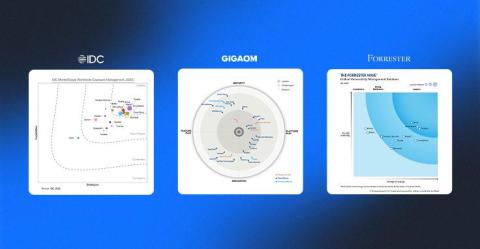
Nucleus Momentum Validated Across Three Industry Analyst Reports
It’s one thing for us to say Nucleus is changing how enterprises address vulnerability and exposure management. It’s another when three different analyst firms all say it, and at the same time. In recent weeks, Forrester, IDC, and GigaOm each published their latest market evaluations, recognizing Nucleus in all three. That’s rare validation in a market where many vendors don’t even make the cut for inclusion.