Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
SKILup Day DevSecOps | How To Securely Access Compute Resources In Cloud Environments | Virag Mody
Being Cyber Resilient Is Critical for the Maritime Industry
Cyber-attacks against maritime and shipping organizations are only increasing. Notwithstanding the IMO’s requirement for organizations in this sector to achieve cyber resilience by 2021, more and more entities are being crippled by malicious attacks.
Why Your Org Needs DLP for Slack: Ensuring Long-Term Data Security
Cloud security requires long-term investments to get right. Today’s demands of remote work and collaboration across teams are forcing security leaders to make fast decisions about which business tools they should allow their orgs to adopt. Data loss prevention (DLP) is a good way to support cybersecurity policies that will safeguard sensitive data and perform at the highest levels of security over the long haul.
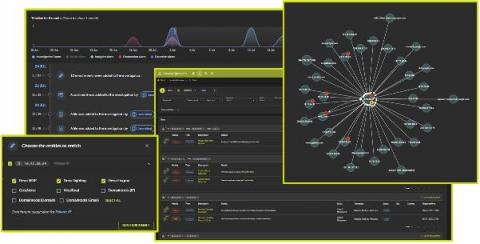
The Devo Cloud-Native SIEM Is Now Even Better
Since February, when we launched Devo Security Operations, the industry’s first cloud-native next-gen SIEM, we’ve kept our foot firmly pressed on the development pedal to add features and enhancements. Security Operations enables customers to transform their security operations centers (SOC) and protect their enterprises against cyberthreats.
ELK - Not Just For The Nice Visitors
Most of the applications we see for the ELK stack are from businesses which want to improve their customers' experience. To return relevant search results and to create Kibana dashboards that allow them to analyse data and give the customers what they want. But there are some cases where the customer is always wrong, and where the last thing you want to do is give a site visitor what he wants. Welcome to the world of forensics, compliance and fraud detection.
Cyber safety tips for virtual events
Since the start of the Covid-19 pandemic, the use of video chat software like Zoom has increased to 300 million meetings held per day. Unfortunately, hackers have taken to crashing private meetings and flooding them with objectionable content — a phenomenon known as Zoombombing. If you’re planning a virtual event, it’s important to pay attention to potential security issues and follow safety tips to keep the experience as safe and secure as possible for everyone involved.
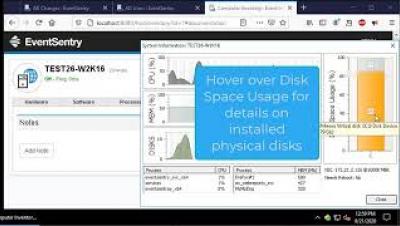
EventSentry's tray application "EventSentray"
Focus on Fixing, Not Just Finding, Vulnerabilities
When investing in an application security (AppSec) program, you expect to see a return on your investment. But in order to recognize a return, your organization needs to determine what success looks like and find a way to measure and prove that the program is meeting your definition of success.
How CISOs Can Foster Effective Comms and Build a Cybersecurity Program
For many organizations, security flows from the top down. That’s a problem when executives don’t emphasize security as much as they should. Cisco learned as much in its CISO Benchmark Study “Securing What’s Now and What’s Next20 Cybersecurity Considerations for 2020.” Here are just some of the findings from Cisco’s study: The reason for these findings wasn’t immediately apparent from Cisco’s study.
2020 Data Governance Trends Report: New Risks, New Rewards of Remote Work
In August 2020, Egnyte partnered with Wakefield Research to survey 400 C-Level IT executives from across the U.S.* to understand how the remote work revolution is changing their governance strategies, and what they’re doing to get ahead of this sea change.