Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Monitor User Activity
Every company monitors their employees to some extent. In the past, companies may have relied solely on time sheets and surveillance footage to keep an eye on their employees. But these tools cannot be used to track what employees are doing on their company-owned computers, smartphones, and tablets. To monitor these devices, managers must turn to more sophisticated tools such as monitoring software.
DevSecOps Insights 2020
Modern Application Development Security
Introducing Teramind BI Reports
Top 10 Most Critical CVEs Added in 2020
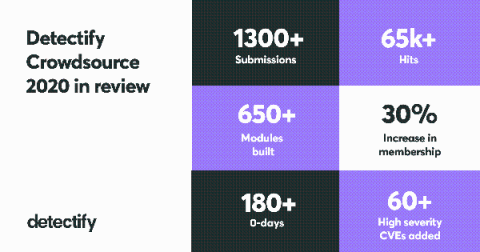
Our global community of hand-picked Detectify Crowdsource ethical hackers are the reason we are able to automate security research so quickly to protect web applications from attack. This past year, we received a record 1300+ submissions from the community including over 180 zero-day vulnerabilities! Every module and security test we build from these hacker-submitted vulnerabilities helps us make the internet more secure.
Appknox Year in Review 2020
How Netskope Can Help with Your 10 Critical Security Project - Nos. 3-4
The annual list of top security projects from Gartner provides key insights on where security leaders should focus their limited time and resources to be the most effective at protecting their data, users, and infrastructure. Netskope provides value for each of the top 10 recommended security projects for this year and next, including many critical capabilities. This blog series will highlight each Gartner recommendation and how Netskope specifically can help.
Why Should I Be Worried About BlueKeep (CVE-2019-0708)
The BlueKeep RDP vulnerability (CVE-2019-0708) is a remote code execution flaw that affects approximately one million systems (as at 29 May 2019) running older versions of Microsoft operating systems. Attention shifted to BlueKeep about two weeks ago, during Microsoft's May 2019 Patch Tuesday. Microsoft released patches but their warning that the vulnerability is wormable drew the attention of security researchers who have uncovered more concerning findings about this emerging threat.
2020: IT Security Lessons to Learn
The year 2020 reshaped business processes and accelerated changes in the way we work, communicate and live. The shift to remote work put a lot of strain on business processes, IT departments and security teams, and cybercriminals used panic and chaos to exploit the situation. Here, we analyze the experiences of the past year and explore the most important challenges we should be prepared for in 2021, as well as share some comments from IT security pros.
5 Best practices for ensuring secure container images
Most modern organizations understand that the earlier you integrate security into the development process, the more secure the applications will be in production. For containerized workloads, securing the container image throughout the application life cycle is a critical part of security, but many organizations don’t even follow basic best practices for ensuring secure container images.