Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The Importance of Speed During Detection and Response: Iranian-Backed Hackers Targeting U.S. Companies with Ransomware
Iranian government-sponsored advanced persistent threat (APT) actors are exploiting known Microsoft and Fortinet vulnerabilities to attack targets with ransomware in the transportation, healthcare and public health sectors, according to an alert issued on Nov. 17 by the Cybersecurity and Infrastructure Security Agency (CISA).
Make the Headlines for Good News - Not a Security Mishap Due to Config Drift
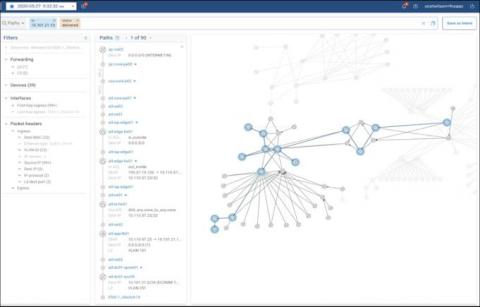
The risk of config drift is ever present. And when you consider that modern enterprises have incredibly complex and ever-changing networks with thousands of devices, from routers to firewalls to switches, running billions of lines of config, it’s easy to understand why. Networks are constantly being changed by people - who though well intentioned - make mistakes. A configuration change that accomplishes the immediate goal may take the network out of compliance, but how would anyone know?
The Top Business Technology Trends for 2021-2022
With the new year just around the corner, the world of business is set to see great change. From 5G and the Internet of Things to the blockchain, new technology trends are creating a digital transformation for companies on a global level. In this article, we’ll take a look at the latest trends in technology to keep an eye out for in 2022 and beyond.
CalCom Software Solutions is Now CIS SecureSuite Product Vendor Member
Splunk SOAR Playbooks: Suspicious Email Domain Enrichment
Splunk SOAR Feature Overview: Visual Playbook Editor + Input Playbooks
Cybersecurity for Oil and Gas: An Overview
The growing value of business data, the vulnerability of networked systems, and the importance of fuel infrastructure have made oil and gas companies major targets for malicious hackers. Already, the industry has been the victim of several high-profile attacks. The Colonial Pipeline hack compromised the business’s networks, shut down its operations, and deprived the East Coast of a pipeline that supplies nearly half the region’s fuel.
Discover PII Data in Microsoft Exchange Online With Egnyte
Your organization runs on information, and much of that information is sensitive. You need consistent governance policies to protect users and data, but just protecting files is not enough. You also need to be able to scan your documents quickly and easily to find personally identifiable information (PII). More than three-quarters of companies have files housed in email repositories, and these often contain customer PII, health records, and other sensitive information.
Introducing Nightfall for Jira, with Real-Time Data Loss Prevention
We’re excited to announce that Nightfall DLP for Jira now has real-time detection. Services like Jira, which are part of the Atlassian ecosystem, are among some of the most popular cloud tools leveraged by companies today. Like most SaaS applications, Jira is an always-on service where many collaborators share information. In some cases, this may result in the unintentional exposure of sensitive data.
Debunking the Myths about Air Gaps
The air gap, a cybersecurity countermeasure that isolates digital assets to put them out of reach of malicious actors, is the subject of many industry myths. Are you confused by all the myths around air gaps? Does it seem odd that logical air gaps are not considered air gaps in spite of their ability to defend against attacks? If you answered “yes” to these questions, you're likely not alone.