Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
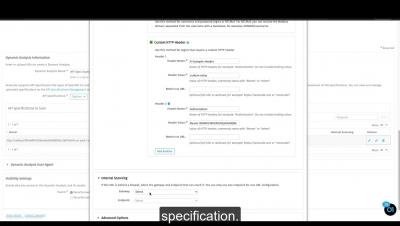
Create an API Specification Scan
Grey's Academy 301: Grey's Academy with GrayMatter
PCI Data Discovery Tools: Keeping Sensitive Data Protected Within Your Organization
The rules set forth by PCI-DSS can seem complicated. Four levels, 12 requirements, multiple credit card brands: it’s easy to get lost in the details of PCI-DSS requirements. However, merchants who fail to meet the PCI compliance standard face heavy consequences. Not only do these companies put their customer data at risk, they also may face hefty fines that can range from $5,000 to $100,000 per month.
Redacting Sensitive Data in 4 Lines of Code
In this tutorial, we’ll demonstrate how easy it is to redact sensitive data and give you a more in-depth look at various redaction techniques, how Nightfall works, and touch upon use cases for redaction techniques. Before we get started, let’s set our Nightfall API key as an environment variable and install our dependencies for our code samples in Python.
Emotet returns: 5 key questions to answer
Who are Stripe OLT...
Nuvias Group Further Invests in Cyber Security and the BeLux Market with Deltalink Acquisition
Privileged account management challenges: comparing PIM, PUM and PAM
Most cyberattacks originate outside the organization. Numerous articles, vulnerability reports, and analytical materials prove this fact. External attacks are usually carried out based on the following scenario: Obviously, it is impossible to provide protection at all stages of an attack using only one type of protection. It is tough to do without a dedicated team and security solutions like firewalls, intrusion detection, antiviruses and more.
How the pandemic made millennials rethink their digital legacies
Before the pandemic, most millennials didn’t have a will, let alone a plan for handing over their digital accounts.
Three-Body Problem for Policy: Policy, Data and Software
In the early days of Styra when we were creating Open Policy Agent (OPA), we had a singular goal in mind: help engineers enforce any policy over any piece of software. We wanted people to be able to write any policy they’d like, whether it be about complex resources managed by Kubernetes or public cloud, APIs routed through gateways or service meshes, data stored in relational or document databases, application deployments controlled by CICD pipelines, and so on.