Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Veracode and Github Integration
Tripwire Experts Offer Point of View on Zero Trust at EO's 6-Month Milestone
When the Biden Administration released its Cybersecurity Executive Order in May 2021, it was clear that Zero Trust would be a central component of the government’s security approach moving forward. Agencies and their partners scrambled to assess their existing Zero Trust investments and the gaps that would need to be filled in order to quickly ramp up implementation.
Secure Your Configurations with Tripwire's Configuration Manager
As cybersecurity professionals, we are always impressing the importance of patch management as one of the best ways to protect systems against vulnerabilities. Sometimes, the vulnerabilities are never fully exploited. Regardless of the threat possibility, patching is one of the easiest ways to ensure the minimum level of security in an organization.
5 Data Loss Prevention Best Practices & Strategies
Data loss prevention (DLP) refers to a category of tools and technologies that classify, detect, and protect information (data) in three states: data in use, data at rest, and data in motion. The purpose of DLP is to enforce corporate data security policies that govern where data does — and doesn’t — belong. As such, there are some key strategies and best practices required to build these data security policies.
6 Cloud Data Loss Prevention Best Practices & Strategies
Data loss prevention (DLP) refers to a category of tools and technologies that classify, detect, and protect information (data) in three states: data in use, data at rest, and data in motion. The purpose of DLP is to enforce corporate data security policies that govern where data does — and doesn’t — belong.
Interview with Cybersecurity Specialist Babak Pasdar, CTO of Acreto
For our latest expert interview on our blog, we’ve welcomed Babak Pasdar to share his thoughts on the topic of cybersecurity and his journey as the CTO of Acreto. Babak Pasdar is a globally recognized innovator, cybersecurity expert, author, and entrepreneur best known for his multiple innovations in the area of cloud security.
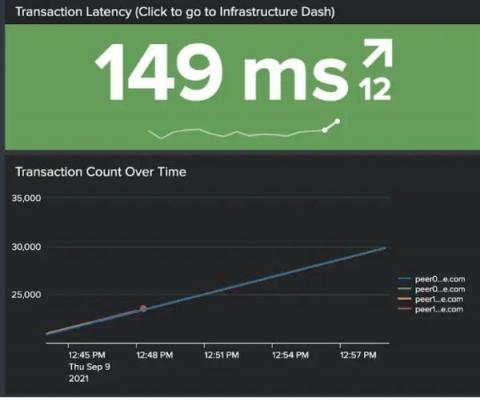
Hyperledger Fabric Security Monitoring with Splunk
In this post, we demonstrate how to set up effective security monitoring of your Hyperledger Fabric infrastructure. We identify some common threats, recognize key data sources to monitor, and walk through using Splunk to ingest and visualize your data. This post follows Introducing Splunk App for Hyperledger Fabric and highlights the use of the app for security monitoring of blockchain infrastructure. We will address smart contract/chaincode security & monitoring in a follow-up post.
Taking back control of the internet, Garry Kasparov and Ondrej Vlcek
The Evolving Threat of Ransomware
Currently, ransomware is the most prominent cyber threat to businesses and individuals. Ransomware attacks are growing more prevalent as cybercriminals find new ways to profit from them. According to CyberEdge’s 2021 Cyberthreat Defense Report, 62% of organizations were victimized by ransomware in 2019—up from 56% in 2018 and 55% in 2017. This rise is arguably fueled by the dramatic increase in ransomware payments.