Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
CurrentWare is Verified as Citrix Ready!
CurrentWare’s suite of user activity monitoring, web filtering, device control, and remote PC power management software has been verified as Citrix Ready®. The Citrix Ready program helps users of Citrix Virtual Apps and Desktops (formerly Citrix XenApp and XenDesktop) identify third-party solutions that are verified as compatible with a Citrix VDI deployment.
Are We Forever Doomed By Software Supply Chain Risks?
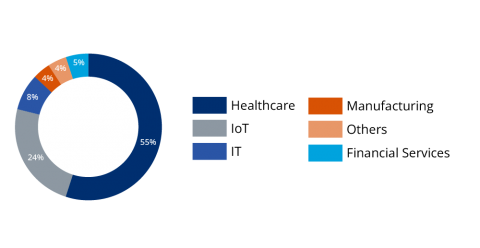
New Supply Chain Vulnerabilities Impact Medical and IoT Devices
Forescout’s Vedere Labs, in partnership with CyberMDX, have discovered a set of seven new vulnerabilities affecting PTC’s Axeda agent, which we are collectively calling Access:7. Three of the vulnerabilities were rated critical by CISA, as they could enable hackers to remotely execute malicious code and take full control of devices, access sensitive data or alter configurations in impacted devices.
The Challenge of Asset Tracking in Industrial Environments
Asset inventory is a significant part of a comprehensive security plan for all organizations. After all, if you do not know what assets you have, then you cannot manage them. Even a small company can amass a surprisingly large amount of assets. It is no surprise that accounting for all of these assets can be like chasing a moving target, as new and old assets must be accounted for, and conversely, decommissioned assets must also be removed.
PHOREAL malware targets the Southeast Asian financial sector
Elastic Security discovered PHOREAL malware, which is targeting Southeast Asia financial organizations, particularly those in the Vietnamese financial sector. Given the continuous pace of malware development, it's no surprise that adversarial groups will leverage successful campaigns as the basis of developing future attacks, and the recently discovered backdoor campaign targeting Vietnamese financial services is no exception.
ISO 27001 compliance: What you need to know in 2022
ISO 27001 (or ISO/IEC 27001) is the leading international standard on information security management. As part of a wider set of related ISO (International Organisation for Standardisation) standards - the ISO 27000 series – it provides a well-defined framework to help any business create, implement, and maintain an effective information security management system (ISMS).
Automated detection and containment with Humio and Tines
The complexity of keeping organizations, customers, and employees safe from cyber threats increases every day. Security teams are often overwhelmed with the need to manage multiple workflows across a myriad of tools. The combination of Humio and Tines helps customers build a clear picture of what's really going on within their environment and automate effective responses at speed and scale.
The women of archTIS share their experience and wisdom as Women in Tech
In honor of International Women’s Day we once again asked the amazingly talented women of archTIS to share their insights as women in tech. This year our Finance and HR leads share their important roles in the company, experiences, and offer advice to young women considering a career in cybersecurity.
Role Based Access Control vs Attribute Based Access Control: Addressing Common Misconceptions
A dynamic, data-centric approach is key to securing sensitive information and achieving compliance in our modern world of hybrid IT solutions, but what are the differences between RBAC vs ABAC the two common access controls approaches? Over the last two years, companies have seen an expedited shift away from using traditional methods to access their data. With more employees working remotely, we find the security controls we have spent years refining are no longer adequate.