Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
15 Minute Friday: How a Leading University Hospital Health System Secures Patient Data with Lookout
CSPM - Intro to Torq Webinar
Strategies For Vendor Third Party Risk Management
How to Protect From Potential Cyber Threats Stemming From Russian/Ukrainian Crisis
Dark Web Insights: Evolving Cyber Tactics Aim to Impact the Russia-Ukraine Conflict
The Russia-Ukraine conflict currently is ongoing and continues to escalate. Trustwave is on heightened alert, and we are actively monitoring malicious cyber activity associated with and adjacent to the conflict between Russia and Ukraine.
Staying safe online when you live off-grid
Over 250,000 people in the US live off the grid, meaning they do not rely on public utilities such as electricity and water. Their aim is generally to live more independently and self-sufficiently, rely on solar or other eco-friendly technologies, and build a stronger connection with nature. However, most people who choose this lifestyle are very much reliant on the Internet.
KapeTriage MindMap for DFIR Practitioners
The Kroll Artifact Parser and Extractor (KAPE) utilizes Targets and Modules to collect and parse digital evidence. Its Compound Targets and Compound Modules call upon other Targets and Modules in order to collect and parse the most important data as efficiently as possible. One of KAPE’s most widely used Compound Targets for incident response (IR) is KapeTriage.
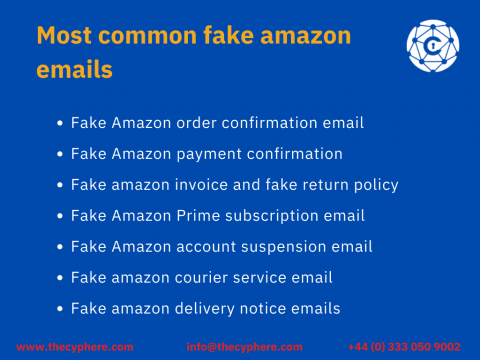
Fake Amazon Emails sent by Hackers: How to prevent Phishing Scams
In the age of fake news and fake emails, fake Amazon emails are becoming a major problem. If you’re not careful, these fake messages will cause some serious problems for your company’s reputation.
Best Practices For Managing Ruby Supply Chain Security Risks
Software supply chain attacks are on the rise – the attacks increased by more than 600% between 2020 and 2021. On RubyGems, the official package repository for the Ruby programming language, attackers usually take advantage of the implicit trust developers have on the gems deployed on the platform and infect them with malicious code.
Regulating a Nation's Information Security Workforce
In a previous article, I examined Australia’s proposed Security Legislation Amendment (Critical Infrastructure) Bill 2020. This information security overhaul imposes strict reporting requirements for enterprises as well as affords the Australian government unprecedented and far-reaching powers that enables them to intervene in the operation of an organisztion’s network in the event of a threat to critical infrastructure.