Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Mitigate the Risk of Ransomware Attacks
Glyptodon Demo
Tigera: Achieving Compliance with PCI, SOC2, GDPR, and more for Containers & Kubernetes
Tigera: AWS Dev Day: Hands-on EKS workshop: Implementing Zero-Trust Security for Containers
Tigera: 4 Ways to Protect Containerized Workloads at runtime
Tigera: How security policies can protect your environment from future vulnerabilities like Log4j
ITOps vs. SecOps vs. DevOps vs. DevSecOps
ITOps, SecOps, and DevOps may sound similar. Indeed, they are similar - to a degree. But they have different areas of focus, different histories, and different operational paradigms. Keep reading for an overview of what ITOps, SecOps, and DevOps mean and how they compare. We'll also explain where DevSecOps fits into the conversation - and why you shouldn't worry so much about defining these terms perfectly as you should about finding ways to operationalize collaboration between your various teams.
EndaceProbe Release Changes the Game for Network Forensics
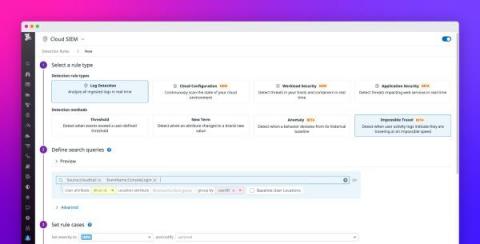
Detect suspicious login activity with impossible travel detection rules
Many modern applications are regularly accessed by countless users from all over the world, which makes it difficult to identify anomalous patterns in login activity indicative of a security breach. This challenge is compounded by the fact that people travel often and regularly access their accounts from new locations. To detect this common attack vector, the Datadog Cloud SIEM now provides the impossible travel detection rule type which helps you spot suspicious logins with confidence.
It's Easier Than You Think: Gaining Visibility Into SaaS Apps To Secure Your Data
Software-as-a-Service (SaaS) apps have become essential to how most of us run our organizations and stay productive — especially over the last two years. On any given day, you’re likely messaging colleagues using Slack or Teams, sharing files with partners from Google Drive or Microsoft SharePoint, or working in Workday or Salesforce to perform an HR- or sales-related business process.