Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Securing the Hybrid Workforce with Netskope Zero Trust Data Protection and Endpoint DLP
Data no longer resides behind the four walls of the traditional enterprise perimeter—it’s everywhere, and can be accessed from seemingly anywhere, thanks to the rapid embrace of cloud by enterprises and the acceleration of hybrid work, or work-from-anywhere, behind the global pandemic.
Why the Cybersecurity Industry Needs to Change Its Siloed Perception
As high-profile data theft incidents continue to rise and become more sophisticated, there is a greater-than-ever need for emerging businesses to take their cybersecurity seriously. So, why do many entrepreneurs and “startup unicorns” consider it the turf of large-scale organizations only, even after some of the world’s largest corporations have fallen prey to cybercrime? Security breaches at so many companies exposed the personal data of millions of Americans.
Your Password Was Exposed in a Non-Google Data Breach: How to Respond
If you’re a Google Chrome user, you may have received the pop-up alert “Your password was exposed in a non-Google data breach” in your web browser. The alert informs users of any recent security breaches which may have compromised their account passwords. Read on to learn more about what this alert means for your data security and the appropriate steps to secure your personal data.
Weekly Cyber Security News 20/05/2022
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. I have a strange bunch this week, the first is a really disturbing crypto mugging which I really hope does not become a new trend.
Reduce spending on Splunk and other high-cost security data solutions through LimaCharlie
Credit Card Fraud Investigation: State of Underground Card Shops in 2022
In our latest credit card fraud investigation blog our threat intelligence analysts investigate the current card shop ecosystem, from active shops and the return of Rescator as well as other recently shuttered card shops and credit card fraud to look out for. Methodology Credit Card Fraud Investigation: Active Card Shops Credit Card Fraud Investigation: Inactive Card Shops Conclusions
Finding CVE-2022-22954 with Zeek
CISA released a warning to federal agencies on May 18 that APT actors are actively exploiting recent vulnerabilities found in VMware, including CVE-2022-22954. Your first thought may have been to want new signatures, indicators, and/or behavioral techniques to detect attempted and successful exploits. If you’re a Zeek user or Corelight customer, you’ll find that sometimes you’re already getting what you need.
Outsourcing your SOC
With businesses constantly at risk of cyber threats, leveraging a Security Operations Centre (SOC) is one way for organisations to proactively monitor and manage their threat landscape. Whether it’s in-house or outsourced, a SOC can help companies implement a process-driven security framework that secures business information against the constant threat of a cyber attack.
Mirai Malware Variants for Linux Double Down on Stronger Chips in Q1 2022
Popular for compromising internet-connected devices and conducting distributed denial of service (DDoS) attacks, Mirai malware variants have been known to compromise devices that run on Linux builds ranging from mobile and Internet of Things (IoT) devices to cloud infrastructures.
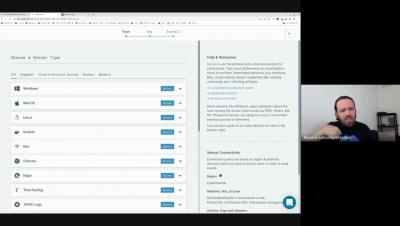
How to access AWS Console using AWS IAM
This blog post explores the traditional authentication and authorization processes to AWS Management Console, and how Teleport can replace them to further secure and audit your Infrastructure Access for AWS. You can access your AWS Management Console through a variety of methods. If a user has AWS Administrator or Root Access, they can see and edit all infrastructure in its entirety. AWS has multiple tools available to mitigate access, but are they enough?