Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Building a simple dynamic job scheduler with Sidekiq
One commonly used feature with Tines is the ability to configure your Actions to run on a schedule (docs). For example, an HTTP Request Action that runs every minute, once a day, or every few hours. Our customers rely heavily on this feature in carrying out their mission-critical workflows. In this post, we examine how our old job scheduler system worked, a very interesting race condition, and why we replaced our old scheduler with something more reliable to meet our delivery guarantees.
Keeping your Kubernetes Backup Data Private with Azure Private Link
At CloudCasa, as a cloud-native backup-as-a-service provider, we are often dealing with customer concerns about the security and privacy of their data. Sometimes the concern is almost paradoxical because the data and application they are protecting is publicly accessible and running inside the public cloud. However, there are times when organizations use public cloud infrastructure with a network architecture that resembles a private cloud.
Is It Really That Easy for MSPs to Consolidate to One Security Vendor?
Gartner predicted that in three years, “80% of enterprises will have adopted a strategy to unify web, cloud services and private application access from a single vendor’s security service edge (SSE) platform.” It seems like it wasn’t too long ago that the security industry was recommending multiple vendors to safeguard your business. Now the pendulum swings the other way. Fortunately, it’s a healthy sign for the cybersecurity industry.
Unlock the Power of Security Automation: 3 Use Cases to Consider
At ThreatQuotient, we write a lot about security automation. Most recently, we’ve discussed how our data-driven approach to automation helps enable extended detection and response (XDR) in all phases of security operations including detection, investigation and response.
How To Integrate Endpoint DLP Into Your Company's Security Policy
Even before the pandemic, many companies had a relaxed approach to the devices employees brought to work. In fact, many businesses had BYOD (bring your own device) policies that allowed team members to work on personal laptops or cell phones. By one account, 75% of employees use their personal cell phones for work. The rise of remote work has only escalated the use of tablets, laptops, and mobile phones for professional use.
Data Loss Prevention: Fundamentals and Best Practices
Every year, business owners grapple with the same question: how can I keep my data safe? The cost of a data leak can quickly escalate to over $7 million per incident, not to mention the damage to a business’s brand reputation and competitive advantage. And, unfortunately, cyber attacks are getting more sophisticated every year. There are many solutions on the market to help businesses protect their information.
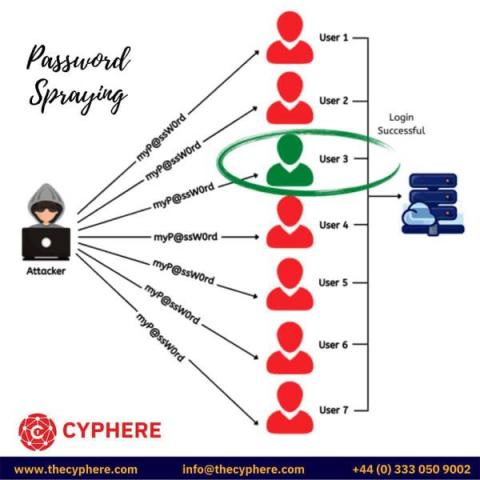
What is a Brute Force Attack? Tools, Examples & Prevention steps
Passwords are an easy way to implement an authentication mechanism in which the user is asked to enter a string of characters (that he had chosen) to log in to his accounts. We will cover brute force attacks, types and examples in this blog article.
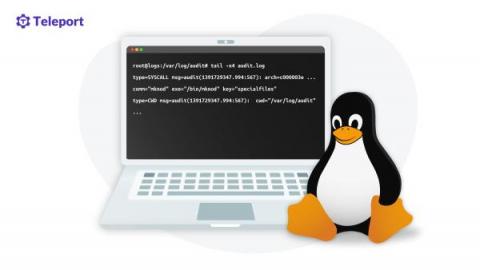
What You Need to Know About Linux Auditing
None of us want to look into a production audit system, as this most likely happens after a security breach or a security incident. Over the years, people have come up with many ideas to see what applications are doing. Almost all databases keep event logs to prevent data loss. Systems such as Kubernetes generate events for every action, and applications that probably run in your production also implement some structured logging for the same reason. But what can we do if all of that is not enough?
Machine Learning, AI, & Cyber Security Part 2: Malicious Actors | Razorwire Podcast
Rethinking security roles and organizational structure for the cloud
As more and more applications and application development move to the cloud, traditional security roles and organizational structures are being shaken up. Why is that and what are the benefits of a cloud-first approach for business?