How to Achieve Encrypted Traffic Visibility and Monitoring Without Breaking Privacy
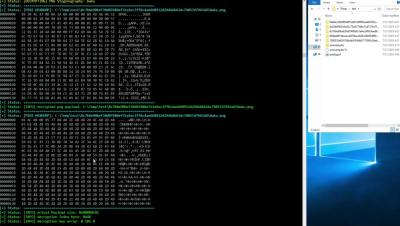
In today’s networks, more than 90% of traffic is encrypted, obscuring both legitimate business data and increasingly sophisticated threats. Forcing every TLS/SSL stream through decryption tools introduces latency, privacy risks, and compliance headaches—so many teams simply turn off inspection and leave dangerous blind spots. Security teams urgently need an encrypted traffic inspection that delivers full encrypted traffic visibility without ever breaking end-to-end encryption.