Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CREST and Immersive Labs announce partnership for developing technical cyber security skills
CREST and Hack The Box partner for cyber security skills development
Cloud Distribution Ltd to Distribute the Full Ivanti Portfolio in the UK
SecureAge Technology launches CatchPulse software for complete protection against malware
Proactive Threat Hunting Bears Fruit: Falcon OverWatch Detects Novel IceApple Post-Exploitation Framework
A Quick Guide To Information Security Programs
Broadly speaking, an information security program is a set of activities and initiatives that support a company’s information technology while protecting the security of business data and enabling the company to accomplish its business objectives. An information security program safeguards the proprietary information of the business and its customers. The Gramm-Leach-Bliley Act (GLBA) has a more specific definition of what a security information program should entail.
Server hardening, why should you automate it?
Spotting Log4j traffic in Kubernetes environments
Editor’s note: This is the latest in a series of posts we have planned over the next several weeks where we explore topics such as network monitoring in Kubernetes, using sidecars to sniff and tunnel traffic, show a real-world example of detecting malicious traffic between containers, and more! Please subscribe to the blog, or come back for more each week.
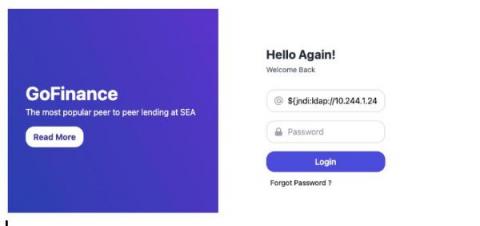
FTSE 100 credential theft study 2022
Corporate credential theft is a targeted effort and makes FTSE 100 companies credentials particularly attractive to cybercriminals with accelerated digital transformation (BYOD and hybrid working). Once an attacker gets hold of stolen user credentials and passwords, they can sell the credentials in the cybercrime underground or use them to compromise an organization’s network, bypassing security measures and threaten the credibility and integrity of the institution.