Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Risks and Challenges of Mismanaged Secrets
Poor secrets management leads to data breaches that can result in compromised credentials, a damaged reputation and millions of dollars in mitigation costs, legal fees and lost revenue. Secrets are non-human privileged credentials that provide access to sensitive information, systems and services. Types of secrets include database passwords, SSH keys, API keys and encryption keys.
What is a Security Breach?
A security breach is when an incident occurs that results in unauthorized access to sensitive data, applications, networks or devices. Typically, when a security breach happens the intruder is able to bypass security measures that were put in place to keep them out. As a result of a security breach, a company or organization’s public image suffers, which can lead to the company losing money. The company or organization could also suffer legal consequences.
Cockroach Labs and Teleport - Hyper-Scale Your Database Without Sacrificing Security
According to a recent Gartner study, the fast pace of change across technologies, organizational priorities, business opportunities and risks requires identity and access management architectures to be more flexible. As digital business relies on digital trust, security and identity are — more than ever — an essential foundation of an organization’s business ecosystem.
What are Tabletop Exercises? How They Can Improve Your Cyber Posture
According to the latest IBM Cost of a Data Breach Report, the average breach costs $4.35M per incident, climbing by 12.7% from 3.86 million USD in IBM’s 2020 report. This does not account for lost business opportunities and lingering reputational damage. A cybersecurity tabletop exercise could substantially reduce this amount simply by having a well-thought-out incident response plan and effectively exercising business continuity plans.
What are Elastic Security capabilities in the cloud - and how do they drive results?
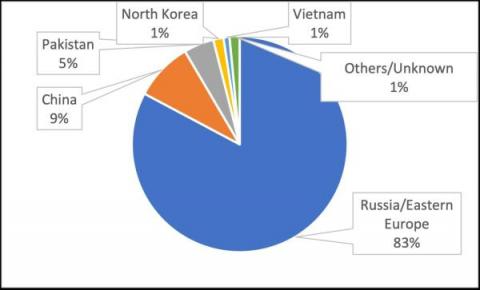
Cyberthreat Trends in 2022H1: Threat Actors Observed, New Malware and Active Hacking Groups
In our companion blog post, Vedere Labs analyzed the main ransomware trends we observed in the first half of 2022, including state-sponsored ransomware, new mainstream targets and evolving extortion techniques. Ransomware is the main threat targeting most organizations nowadays. However, three other notable cyberthreat trends also evolved during this period: Below we analyze each of these trends in more detail.
De-risking Code with Snyk and Codecov
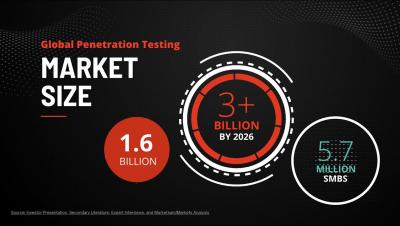
The Pitch That Earned Vonahi 1 of The Top 3 Pitch IT Finalist Spots
The ClubCISO report reveals a fundamental shift in security culture
With business and technology becoming increasingly intertwined, organizations are being forced to rethink how they look at digital security. Once overlooked or viewed as a mere afterthought, today it has become a business-critical necessity. As a result, organizations across industry lines are racing to improve their security postures.