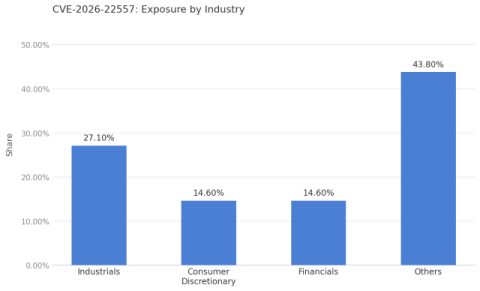
Emerging Threat: Ubiquiti UniFi Network Application Path Traversal (CVE-2026-22557)
CVE-2026-22557 is a path traversal vulnerability in the Ubiquiti UniFi Network Application caused by improper limitation of a pathname to a restricted directory (CWE-22). A malicious actor with network access can exploit the flaw to traverse directory boundaries, access files on the underlying operating system, and manipulate those files to gain unauthorized access to system accounts.