Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Kroll named as winner at Computing Security Awards 2022
CrowdStrike and Google Chrome: Building an Integrated Ecosystem to Secure Your Enterprise Using the Power of Log Management
Organizations today face an onslaught of attacks across devices, identity and cloud workloads. The more security telemetry an organization has to work with, the better threat hunters can contextualize events to find and remediate potential threats. Google recently announced Chrome Enterprise Connectors Framework, a collection of plug-and-play integrations with industry-leading security solution providers.
How to validate Kubernetes YAML files?
Citrix's Corey Hill: How to make mental health a priority for your security team
In our latest episode of the Future of Security Operations podcast, Thomas speaks to Corey Hill, Director of Security Operations and Incident Response at Citrix. After working at organizations such as Mandiant and Cisco, Corey joined Citrix in 2020 when there were just a handful of people on the SOC team.
Searching Data: List View
How to Keep Your Data Secure as a Digital Nomad
Now that remote work has become the norm, employees are taking advantage of this opportunity to travel the globe and work from anywhere in the world—as long as it’s within company policy. With the rise of digital nomads, it is important that you know how to keep yourself safe from cyberattacks when working remotely from city to city. This blog will help you understand what you need to do to secure your data as a digital nomad.
JFrog's Advanced Security Scanners Discovered Thousands of Publicly Exposed API Tokens - And They're Active
The JFrog Security Research team released the findings of a recent investigation wherein they uncovered thousands of publicly exposed, active API tokens. This was accomplished while the team tested the new Secrets Detection feature in the company’s JFrog Advanced Security solution, part of JFrog Xray.
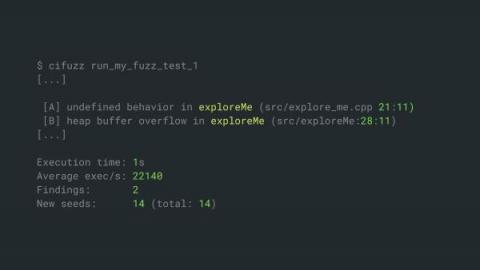
How to Simplify Fuzz Testing for C++
Today I want to show you a way to simplify fuzz testing for your C++ applications. If you read this article to the end, you will learn about an automated testing approach that can protect your applications against all sorts of memory corruptions and other security vulnerabilities.
The Myths and Truths of Employee Monitoring
Early in the pandemic, searches related to “how to monitor employees working from home” increased by 1,705%. Without the oversight of managers in an office setting, many companies are concerned that their employees are less productive, and that there is an increase risk to the company. This is a major reason why the use of employee monitoring technology has soared in the past year.