Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What is Data Exfiltration and How Can You Prevent It?
Every day, cybercriminals are seeking new techniques to extract data and infiltrate networks; one of these techniques is data exfiltration. To prevent these kinds of cyber threats, we must learn how data exfiltration works, the methods used to execute attacks, and how companies can secure their network from further data breaches. Let’s take a closer look.
ICYMI: How to Ensure Continuous Data Security & Compliance across your SaaS Apps
We recently hosted a live discussion covering emerging trends within the cloud security space, primarily reflecting on how organizations could adopt a posture of continuous security and compliance across their SaaS applications. Continue on below to view the highlights from this discussion.
Teleport Demo - 30 Minute Overview
0:00 Intro
1:00 Architecture Overview
3:00 Single Sign On Integration
5:00 Teleport Server Access
7:00 tsh and session recordings
9:00 Teleport App Access
11:00 RBAC Mapping
12:05 Teleport K8s Access
15:00 Teleport DB Access
18:00 Teleport RDP Access
22:00 Access Requests
24:00 Teleport Slackbot
26:00 Active Session Joining
27:00: Trusted Clusters
28:00 Open Source vs Enterprise
Exploring Security and Observability on Splunk Lantern
Your organization purchased Splunk Cloud Platform some time ago. Your environment is ingesting dozens of data sources and your team has expert level SPL skills. You've created easily consumable dashboards and reports for many different types of stakeholders and you've mastered alert fatigue. Your organization's return on investment both in Splunk and Splunk education is paying large dividends in terms of time saved managing threats and improved operational efficiency.
Entering the 7th month of 2022 with 7 prestigious Grand Globee awards
ManageEngine is the proud winner in seven categories of the Information Technology World Awards, the IT industry’s premiere excellence award program. We are honored to be recognized by the only complete IT recognition and achievement award program that covers all the facets of the IT industry. More than 170 judges consisting of industry experts in IT and cybersecurity from around the world were a part of the jury.
Cyber risk management platform Outpost24 joins forces with international investment firm Vitruvian Partners for further global expansion
Tips for Managing Unstructured Data Security
All information is an attractive target for bad actors, but some is inherently more valuable than others. State-sponsored and hacktivist attacks constantly probe enterprise networks seeking to identify the location of sensitive information. Attackers historically targeted core enterprise systems but as the defenses for those systems have matured, attackers now target the same information but in less secured unstructured (broadly speaking, file and email based) repositories.
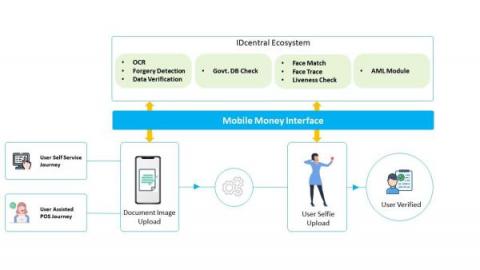
An Alleged 22 Billion Mobile Money Fraud
As per the news reports published MTN’s Mobile Money Bank suffers N22B Fraud, Drags 18 Banks to court for recovery The newly licensed Mobile Money Payment Service Bank Limited (MOMO PSB) a banking subsidiary of MTN Communications Limited has in less than a month operation suffered a massive fraud worth over N22 billion on its network. The suspicious transfers were due to the fact that the MoMo PSB suffered system exploitation which led to the said debits.