Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
White House Memo Takes on Securing Critical Infrastructure Control Systems
Attacks targeting critical infrastructure have been on the rise in recent years. Back in 2019, for instance, 56% of utility professionals responsible for overseeing risk in their organizations’ operational technology (OT) assets told Siemens and the Ponemon Institute that they experience at least one shutdown or operational data loss event a year.
Limitless XDR defined: Ingest, retain, and analyze security data freely
Elastic Security's newest features define the potential of XDR for cybersecurity teams. Our single platform brings together SIEM and endpoint security, allowing users to ingest and retain large volumes of data from diverse sources, store and search data for longer, and augment threat hunting with detections and machine learning. Security vendors are using the term “XDR” with increasing frequency, applying varied definitions to suit their respective technologies.
Elastic 7.14.0 introduces the industry's first free and open Limitless XDR
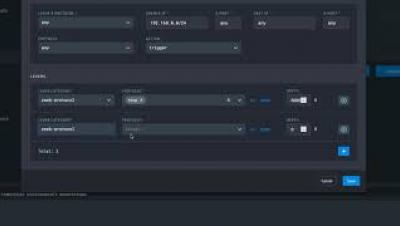
We are pleased to announce the general availability (GA) of Elastic 7.14, including our Elastic Enterprise Search, Observability, and Security solutions, which are built into the Elastic Stack — Elasticsearch and Kibana. Elastic 7.14 empowers organizations with the first free and open Limitless XDR, which delivers unified SIEM and endpoint security capabilities in one platform.
Why Cybersecurity is Critical to Maintaining HIPAA Compliance
When exploringhttps://securityscorecard.com/admin/entries/blog/154640?draftId=2332&fresh=1# top network security breaches, many think of the obvious: banks or large consumer institutions. However, healthcare organizations are on the rise as a top target for hackers, with the number of data breaches rising 36% in the second half of 2020.
New sophisticated RAT in town: FatalRat analysis
AT&T Alien Labs™ has recently observed the presence of a new remote access trojan (RAT) malware in its threat analysis systems. The malware, known as FatalRAT, appears to be distributed via forums and Telegram channels, hidden in download links that attempt to lure the user via software or media articles.
The best security advice from 100 episodes of The Secure Developer podcast
Technology, culture, and process all have to change to ensure safe software is delivered faster. It’s a lot to tackle. But you don’t have to do it alone. The Secure Developer, a podcast from Snyk’s founder Guy Podjarny, just hit 100 episodes of thought-provoking conversations with security experts at a wide cross-section of companies.
Detectify developing API security testing with fuzzing
PKI encryption - a crash course
With work-from-home now the default mode in most industries, organisations and employees now have to access and transfer files across home networks and personal devices on a daily basis. Naturally businesses are concerned as leaked files can have serious financial and legal repercussions.